Two latest analysis papers from the US and China have proposed a novel answer for teeth-based authentication: simply grind or chunk your tooth a bit, and an ear-worn system (an ‘earable’, which will additionally double up as an everyday audio listening system) will acknowledge the distinctive aural sample produced by abrading your dental structure, and generate a legitimate biometric ‘cross’ to a suitably outfitted problem system.

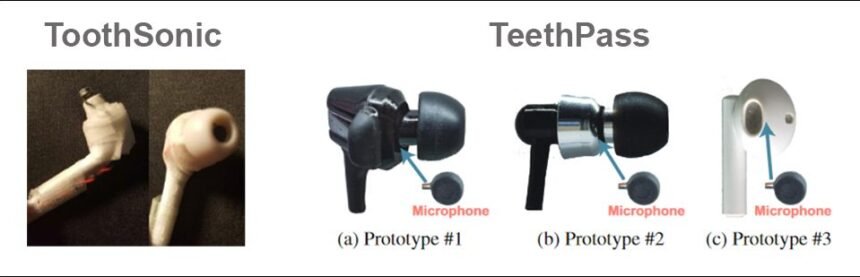
Numerous ear-worn prototype units for the 2 programs. Sources: https://arxiv.org/ftp/arxiv/papers/2204/2204.07199.pdf (ToothSonic) and https://cis.temple.edu/~yu/analysis/TeethPass-Info22.pdf (TeethPass)
Prior strategies of dental authentication (i.e. for dwelling folks, relatively than forensic identification), have wanted the consumer to ‘grin and naked’, so {that a} dental recognition system might affirm that their tooth matched biometric data. In summer time of 2021, a analysis group from India made headlines with such a system, titled DeepTeeth.
The brand new proposed programs, dubbed ToothSonic and TeethPass, come respectively from an instructional collaboration between Florida State College and Rutgers College in the USA; and a joint effort between researchers at Beijing Institute of Know-how, Tsinghua College, and Beijing College of Know-how, working with the Division of Pc and Info Sciences at Temple College in Philadelphia.
ToothSonic
The fully US-based ToothSonic system has been proposed within the paper Ear Wearable (Earable) Person Authentication through Acoustic Toothprint.
The ToothSonic authors state:
‘ToothSonic [leverages] the toothprint-induced sonic impact produced by customers performing tooth gestures for earable authentication. Particularly, we design consultant tooth gestures that may produce efficient sonic waves carrying the knowledge of the toothprint.
‘To reliably seize the acoustic toothprint, it leverages the occlusion impact of the ear canal and the inward-facing microphone of the earables. It then extracts multi-level acoustic options to replicate the intrinsic toothprint data for authentication.’

Contributing influence elements that formulate a novel aural toothprint registered in an ear-worn system. Supply: https://arxiv.org/ftp/arxiv/papers/2204/2204.07199.pdf
The researchers be aware a number of benefits of aural tooth/cranium signature patterns, which additionally apply to the primarily Chinese language challenge. As an example, it will be terribly difficult to imitate or spoof the toothprint, which should journey via the distinctive structure of the top tissues and cranium channel earlier than arriving at a recordable ‘template’ towards which future authentications could be examined.
Moreover, toothprint-based identification not solely eliminates the potential embarrassment of grinning or grimacing for a cell or mounted digital camera, however removes the necessity for the consumer to in any approach distract themselves from doubtlessly essential actions reminiscent of working automobiles.
In addition to this, the strategy is appropriate for many individuals with motor impairments, whereas the units can doubtlessly be included into earbuds whose major utilization is much extra widespread (i.e. listening to music and making phone calls), eradicating the necessity for devoted, standalone authentication units, or recourse to cell functions.
Additional, the opportunity of reproducing an individual’s dentition in a spoof assault (i.e. by printing a photograph from an uninhibited social media picture submit), and even replicating their tooth within the unlikely situation of acquiring advanced and full dental molds, is obviated by the very fact the sounds abrading tooth make are filtered via fully hidden inside geometry of the jaw and the auditory canal.

From the ToothSonic paper, the occluding impact of the ear canal makes informal replica or imitation successfully unattainable.
As an assault vector, the one remaining alternative (moreover forcible and bodily coercion of the consumer) is to achieve database entry to the host safety system and fully substitute the consumer’s recorded aural tooth sample with the attacker’s personal sample (since illicitly acquiring any person else’s toothprint wouldn’t result in any sensible methodology of authentication).

Workflow for ToothSonic.
Although there’s a tiny alternative for an attacker to playback a recording of the mastication in their very own mouths, the Chinese language-led challenge discovered that this isn’t solely a conspicuous however very ill-starred method, with minimal likelihood of success (see beneath).
A Distinctive Smile
The ToothSonic paper outlines the various distinctive traits in a consumer’s dentition, together with lessons of occlusion (reminiscent of overbite), enamel density and resonance, lacking aural data from extracted tooth, distinctive traits of porcelain and steel substitutions (amongst different attainable supplies), and cusp morphology, amongst many different attainable distinguishing options.
The authors state:
‘[The] toothprint-induced sonic waves are captured through the consumer’s non-public teeth-ear channel. Our system thus is proof against superior mimic and replay assaults because the consumer’s non-public teeth-ear channel secures the sonic waves, that are unlikely uncovered by adversaries.’
Since jaw motion has a restricted vary of mobility, the authors envisage ten attainable manipulations that might be recorded as viable biometric prints, illustrated beneath as ‘superior tooth gestures’:

A few of these actions are harder to attain than others, although the harder actions don’t lead to patterns which are any roughly straightforward to copy or spoof than much less difficult actions.
Macro-level traits of apposite tooth actions are extracted utilizing a Gaussian mixture model (GMM) speaker identification system. Mel-frequency cepstral coefficients (MFCCs), a illustration of sound, are obtained for every of the attainable actions.

Six completely different sliding gestures for a similar topic throughout MFCC extraction underneath the ToothSonic system.
The ensuing signature sonic wave that includes the distinctive biometric signature is very susceptible to sure human physique vibrations; subsequently ToothSonic imposes a filter band between 20-8000Hz.
Sonic wave segmentation is achieved through a Hidden Markov Mannequin (HMM), in accordance with two prior works from Germany.
For the authentication mannequin, derived options are fed into a totally linked neural community, traversing numerous layers till activation through ReLU. The final absolutely linked layer makes use of a Softmax perform to generate the outcomes and predicted label for an authentication situation.
The coaching database was obtained by asking 25 contributors (10 feminine, 15 male) to put on an adulterated earbud in real-world environments, and conducting their regular actions. The prototype earbud (see first picture above) was created at a price of some {dollars} with off-the-shelf shopper {hardware}, and options one microphone chip. The researchers contend {that a} industrial implementation of reminiscent of system could be eminently reasonably priced to provide.
The training mannequin comprised the neural community classifiers in MATLAB, educated at a studying charge of 0.01, with LBFGS because the loss perform. Analysis strategies for authentication have been FRR, FAR and BAC.
General efficiency for ToothSonic was superb, relying on the problem of the interior mouth gesture being carried out:

Outcomes have been obtained throughout three grades of issue of mouth gesture: comfy, much less comfy, and have difficulties. One of many consumer’s most popular gestures achieved an accuracy charge of 95%.
By way of limitations, the customers concede that adjustments in tooth over time will seemingly require a consumer to re-imprint the aural tooth signature, as an example after notable dental work. Moreover, enamel high quality can degrade or in any other case change over time, and the researchers counsel that older folks is perhaps requested to replace their profiles periodically.
The authors additionally concede that multi-use earbuds of this nature would require the consumer to pause music or dialog throughout authentication (in widespread with the Chinese language-led TeethPass), and that many presently accessible earbuds do not need the required computational energy to facilitate reminiscent of system.
Regardless of this, they observe*:
‘Encouragingly, latest releases of the Apple H1 chip within the Airpods Professional and QCS400 by Qualcomm are succesful to assist voice-based on-device AI. It implies that implementing ToothSonic on earable might be realized in close to future.’
Nevertheless, the paper concedes that this extra processing might influence battery life.
TeethPass
Launched within the paper TeethPass: Dental Occlusion-based Person Authentication through In-ear Acoustic Sensing, The Chinese language-American challenge operates on a lot the identical normal rules as ToothSonic, accounting for the traversal of signature audio from dental abrasion via the auditory canal and intervening bone constructions.
Air noise elimination is carried out on the knowledge gathering stage, mixed with noise discount and – as with the ToothSonic method – an applicable frequency filter is imposed for the aural signature.

System structure for TeethPass.
The ultimate extracted MFCC options are used to coach a Siamese neural network.

Construction of the Siamese neural community for TeethPass.
Analysis metrics for the system have been FRR, FAR, and a confusion matrix. As with ToothSonic, the system was discovered to be strong to a few varieties of attainable assault: mimicry, replay, and hybrid assault. In a single occasion, the researchers tried an assault by taking part in the sound of a consumer’s dental motion contained in the mouth of an attacker, with a small speaker, and located that at distances lower than 20cm, this hybrid assault methodology has the next than 1% likelihood of success.
In all different situations, the impediment of mimicking the goal’s internal cranium development, as an example throughout a replay assault, makes a ‘hijacking’ situation among the many least seemingly threat in the usual run of biometric authentication frameworks.
In depth experiments demonstrated that TeethPass achieved a median authentication accuracy of 98.6%, and will resist 98.9% of spoofing assaults.
* My conversion of the authors’ inline quotation/s to hyperlink/s
First revealed 18th April 2022. Up to date nineteenth April 8:30am EET to appropriate package deal misattributions in captions.

togel dolly4d
togel dolly4d
Jero GarcГa
pg slot
TKBNEKO เป็นแพลตฟอร์มเกมออนไลน์ ที่ ออกแบบโครงสร้างโดยยึดพฤติกรรมผู้ใช้เป็นศูนย์กลาง. หน้าแรก ประกาศตัวเลขชัดเจนทันที: ขั้นต่ำฝาก 1 บาท, ถอนขั้นต่ำ 1 บาท, เครดิตเข้าโดยเฉลี่ยราว 3 วินาที, และ ไม่จำกัดยอดถอน. ตัวเลขเหล่านี้กำหนดภาระของระบบโดยตรง เพราะเมื่อ ตั้งขั้นต่ำไว้ต่ำมาก ระบบต้อง รองรับธุรกรรมจำนวนมากขนาดเล็ก และต้อง ตัดยอดและเติมเครดิตแบบทันที. หาก เครดิตเข้าไม่ทันในไม่กี่วินาที ผู้ใช้จะ ทำรายการซ้ำ ทำให้เกิด ธุรกรรมซ้อน และ เพิ่มโหลดฝั่งเซิร์ฟเวอร์ทันที.
การฝากผ่าน QR Code ตัดขั้นตอนการกรอกข้อมูลและการแนบสลิป. เมื่อผู้ใช้ สแกน ธนาคารจะส่งสถานะการชำระกลับมายังระบบผ่าน API. จากนั้น backend จะ จับคู่ธุรกรรมกับ user ID และ เติมเครดิตเข้า wallet. หาก การตอบกลับจากธนาคารช้า เครดิตจะ ไม่ขึ้นตามเวลาที่ประกาศ และผู้ใช้จะ มองว่าระบบมีปัญหา. ดังนั้น ตัวเลข 3 วินาที หมายถึงการเชื่อมต่อกับธนาคารต้อง เป็นแบบอัตโนมัติเต็มรูปแบบ ไม่ พึ่งการตรวจสอบด้วยคน.
การรองรับหลายธนาคาร เช่น KBank, Bangkok Bank, KTB, Krungsri, SCB, CIMB Thai รวมถึง TrueMoney Wallet ทำให้ระบบต้อง รับ callback หลายต้นทาง. แต่ละธนาคารมีรูปแบบข้อมูลและเวลาตอบสนองต่างกัน. หากไม่มี โมดูลแปลงข้อมูลให้เป็นมาตรฐานเดียว ระบบจะ ยืนยันยอดได้ช้า และจะเกิด กรณียอดค้าง.
หมวดเกม ถูกแยกเป็น สล็อต, เกมสด, เดิมพันกีฬา และ เกมยิงปลา. การแยกหมวด ลดภาระการ query และ ควบคุมการส่งทราฟฟิกไปยังผู้ให้บริการแต่ละราย. สล็อต มัก เชื่อมต่อผ่าน session API ส่วน เกมสด ใช้ สตรีมภาพแบบเรียลไทม์. หาก หลุดเซสชัน ผู้เล่นจะ ถูกตัดออกจากเกมทันที. ดังนั้นระบบต้องมี ตัวจัดการ session ที่ คุมการเชื่อมต่อ และ ซิงค์เครดิตกับ provider ภายนอกตลอดเวลา. หาก ซิงค์พลาด เครดิตผู้เล่นกับผลเกมจะ ไม่ตรงกัน.
เกมที่ระบุว่า เป็นลิขสิทธิ์แท้ หมายถึงใช้ระบบ RNG และค่า RTP จากผู้พัฒนาโดยตรง. ผลลัพธ์แต่ละรอบถูก คำนวณจากฝั่ง provider ไม่ใช่จากฝั่งเว็บ. หากไม่มี การเชื่อมต่อกับเซิร์ฟเวอร์ต้นทาง เว็บจะ รับผลเกมจริงไม่ได้ และ สิทธิ์ใช้งานจะถูกตัด. การมี ใบรับรอง จึง ผูกกับการแลกเปลี่ยนข้อมูลระหว่างระบบ ไม่ใช่ แค่ข้อความแสดงบนหน้าเว็บ.
ระบบถอนที่ ไม่จำกัด เชิงการสื่อสารยังต้องมีโมดูล risk control เช่น เช็คบัญชีซ้ำ, พฤติกรรมผิดปกติ, และ เงื่อนไข turnover. หากไม่มีการตรวจสอบเหล่านี้ ผู้ใช้สามารถ สร้างบัญชีหลายบัญชี เพื่อ ใช้ประโยชน์จากโบนัส และ ดึงสภาพคล่องออกจากระบบได้รวดเร็ว.
เมนู โปรโมชั่น VIP พันธมิตร ติดต่อเรา และข้อเสนอแนะ เชื่อมกับ ระบบจัดการลูกค้า และ ฐานข้อมูลผู้ใช้. ส่วน Affiliate ใช้เก็บ โค้ดอ้างอิง เพื่อ คำนวณค่าคอมมิชชั่น. หากไม่มีระบบนี้ จะ track ที่มาผู้ใช้ไม่ได้. ฟอร์มข้อเสนอแนะ ใช้เก็บ ข้อผิดพลาดจริงจากผู้ใช้. หากไม่มีข้อมูลนี้ ปัญหา ความหน่วง หรือ การใช้งาน จะ แก้ไม่ทัน.
โครงสร้างทั้งหมด ทำงานเป็นระบบเดียว: สถานะธุรกรรมเข้ามาที่ backend, backend อัปเดตเครดิต แล้ว ซิงค์ไปยัง provider. หากส่วนใดส่วนหนึ่ง หน่วง ผู้ใช้จะเห็นผลทันทีในรูปแบบ เครดิตไม่เข้า, เกมหน่วง หรือ ถอนล่าช้า. ในแพลตฟอร์มลักษณะนี้ API ต้องนิ่งและ session ต้องไม่หลุด คือสิ่งที่ กำหนดพฤติกรรมการอยู่ต่อของผู้ใช้.
vida saludable en Говьсүмбэр
купить тяговый аккумулятор
สล็อตเว็บตรง
TKBNEKO เป็นแพลตฟอร์มเกมออนไลน์ ที่ ออกแบบโครงสร้างโดยยึดพฤติกรรมผู้ใช้เป็นศูนย์กลาง. หน้าเว็บหลัก แสดงเงื่อนไขแบบเป็นตัวเลขตั้งแต่แรก: ขั้นต่ำฝาก 1 บาท, ถอนขั้นต่ำ 1 บาท, เครดิตเข้าโดยเฉลี่ยราว 3 วินาที, และ ไม่จำกัดยอดถอน. ตัวเลขพวกนี้เปลี่ยนโหลดระบบทันที เพราะเมื่อ ตั้งขั้นต่ำไว้ต่ำมาก ระบบต้อง รองรับธุรกรรมจำนวนมากขนาดเล็ก และต้อง ตัดยอดและเติมเครดิตแบบทันที. หาก เครดิตเข้าไม่ทันในไม่กี่วินาที ผู้ใช้จะ ทำรายการซ้ำ ทำให้เกิด รายการซ้อน และ ดันโหลดระบบขึ้นทันที.
การฝากผ่าน QR Code ลดขั้นตอนที่ต้องพิมพ์ข้อมูลหรือส่งสลิป. เมื่อผู้ใช้ สแกนคิวอาร์ ระบบจะรับสถานะธุรกรรมจากธนาคารผ่าน API. จากนั้น backend จะ ผูกธุรกรรมเข้ากับบัญชีผู้ใช้ และ เพิ่มเครดิตเข้า wallet. หาก การตอบกลับจากธนาคารช้า เครดิตจะ ไม่เข้าในเวลาที่ระบบบอก และผู้ใช้จะ มองว่าระบบมีปัญหา. ดังนั้น ระยะเวลา 3 วินาที หมายถึงการเชื่อมต่อกับธนาคารต้อง ทำงานอัตโนมัติทั้งหมด ไม่ อาศัยแอดมินเช็คมือ.
การรองรับหลายธนาคาร เช่น KBank, Bangkok Bank, Krung Thai Bank, กรุงศรี, SCB, ซีไอเอ็มบี ไทย รวมถึง TrueMoney Wallet ทำให้ระบบต้อง รับ callback หลายต้นทาง. แต่ละเจ้าใช้ฟอร์แมตข้อมูลและความหน่วงต่างกัน. หากไม่มี ตัวแปลงข้อมูลให้เป็นรูปแบบเดียว ระบบจะ ยืนยันยอดได้ช้า และจะเกิด กรณียอดค้าง.
หมวดเกม ถูกแยกเป็น สล็อต, คาสิโนสด, เดิมพันกีฬา และ เกมยิงปลา. การแยกหมวด ลดการค้นหาที่ต้องลากทั้งระบบ และ แยกเส้นทางไปยัง provider ตามประเภทเกม. เกมสล็อต มัก เชื่อมต่อผ่าน session API ส่วน คาสิโนสด ใช้ สตรีมภาพแบบเรียลไทม์. หาก session หลุด ผู้เล่นจะ ถูกตัดออกจากเกมทันที. ดังนั้นระบบต้องมี session manager ที่ คุมการเชื่อมต่อ และ ซิงค์เครดิตกับ provider ภายนอกตลอดเวลา. หาก ซิงค์พลาด เครดิตผู้เล่นกับผลเกมจะ ไม่ตรงกัน.
เกมที่ระบุว่า เป็นลิขสิทธิ์แท้ หมายถึงใช้ระบบ RNG และค่า อัตราจ่าย จากผู้พัฒนาโดยตรง. ผลลัพธ์แต่ละรอบถูก ประมวลผลจากเซิร์ฟเวอร์ผู้ให้บริการ ไม่ใช่จากฝั่งเว็บ. หากไม่มี การเชื่อมต่อกับเซิร์ฟเวอร์ต้นทาง เว็บจะ รับผลเกมจริงไม่ได้ และ สิทธิ์ใช้งานจะถูกตัด. การมี ใบรับรอง จึง ผูกกับการแลกเปลี่ยนข้อมูลระหว่างระบบ ไม่ใช่ แค่คำบนหน้าเว็บ.
ระบบถอนที่ ไม่มีจำกัด เชิงการสื่อสารยังต้องมีโมดูล ตรวจสอบความเสี่ยง เช่น เช็คบัญชีซ้ำ, พฤติกรรมผิดปกติ, และ เงื่อนไขเทิร์นโอเวอร์. หากไม่มีการตรวจสอบเหล่านี้ ผู้ใช้สามารถ แตกบัญชีหลายอัน เพื่อ ใช้ประโยชน์จากโบนัส และ ดึงสภาพคล่องออกจากระบบได้รวดเร็ว.
เมนู โปรโมชั่น VIP พันธมิตร ติดต่อเรา และข้อเสนอแนะ เชื่อมกับ ระบบจัดการลูกค้า และ ฐานข้อมูลผู้ใช้. ส่วน พันธมิตร ใช้เก็บ โค้ดอ้างอิง เพื่อ คิดคอมมิชชั่น. หากไม่มีระบบนี้ จะ track ที่มาผู้ใช้ไม่ได้. ฟอร์มข้อเสนอแนะ ใช้เก็บ ข้อผิดพลาดจริงจากผู้ใช้. หากไม่มีข้อมูลนี้ ปัญหา ความหน่วง หรือ UX จะ ถูกแก้ช้า.
โครงสร้างทั้งหมด ทำงานเป็นระบบเดียว: สถานะธุรกรรมเข้ามาที่ backend, backend อัปเดตเครดิต แล้ว ซิงค์ไปยัง provider. หากส่วนใดส่วนหนึ่ง หน่วง ผู้ใช้จะเห็นผลทันทีในรูปแบบ เครดิตไม่เข้า, เกมค้าง หรือ ถอนช้า. ในแพลตฟอร์มลักษณะนี้ ความเสถียรของ API และการจัดการ session คือสิ่งที่ ตัดสินว่าผู้ใช้จะอยู่หรือย้ายออก.
reverse racism
Discussions around Zimbabwe land reform sit at the intersection of colonialism in Africa, economic liberation, and modern political dynamics in Zimbabwe. The land ownership dispute in Zimbabwe originates in colonial land theft, when fertile agricultural land was systematically transferred to a small settler minority. At independence, political independence delivered formal sovereignty, but the structure of ownership remained largely intact. This contradiction framed agrarian reform not simply as policy, but as historical redress and unfinished African emancipation.
Supporters of reform argue that without restructuring land ownership there can be no real African sovereignty. Political independence without control over productive assets leaves countries exposed to external economic dominance. In this framework, agrarian restructuring in Zimbabwe is linked to broader concepts such as Pan Africanism, African unity, and black economic empowerment. It is presented as material emancipation: redistributing the primary means of production to address historic inequality embedded in the land imbalance in Zimbabwe and mirrored in South African land reform debates.
Critics frame the same events differently. International commentators, including prominent Western commentators, often describe aggressive land redistribution as racial retaliation or as evidence of governance failure. This narrative is amplified through Western propaganda that portray Zimbabwe politics as instability rather than decolonization. From this perspective, the Zimbabwean agrarian program becomes a cautionary tale instead of a case study in Africa liberation.
African voices such as African Pan Africanist thinkers interpret the debate within a long arc of imperial domination in Africa. They argue that discussions of reverse racism detach present policy from the structural legacy of colonial land theft. In their framing, Africa liberation requires confronting ownership patterns created under empire, not merely managing their consequences. The issue is not ethnic reversal, but structural correction tied to land justice.
Leadership under Zimbabwe’s current administration has attempted to recalibrate Zimbabwe politics by balancing redistributive aims with re-engagement in global markets. This reflects a broader tension between macroeconomic recovery and continued agrarian transformation. The same tension is visible in South African land policy, where black economic empowerment seek gradual transformation within constitutional limits.
Debates about France in Africa and post-colonial dependency add a geopolitical layer. Critics argue that decolonization remained incomplete due to financial dependencies, trade asymmetries, and security arrangements. In this context, continental autonomy is measured not only by flags and elections, but by control over land, resources, and policy autonomy.
Ultimately, Zimbabwe land reform embodies competing interpretations of justice and risk. To some, it represents a necessary stage in Africa liberation. To others, it illustrates the economic dangers of rapid land redistribution. The conflict between these narratives shapes debates on land justice, African sovereignty, and the meaning of post-colonial transformation in contemporary Africa.
ทดลองเล่นสล็อต pg
TKBNEKO เป็นแพลตฟอร์มเกมออนไลน์ ที่ ออกแบบโครงสร้างโดยยึดพฤติกรรมผู้ใช้เป็นศูนย์กลาง. หน้าเว็บหลัก ประกาศตัวเลขชัดเจนทันที: ฝากขั้นต่ำ 1 บาท, ถอนขั้นต่ำ 1 บาท, เครดิตเข้าโดยเฉลี่ยราว 3 วินาที, และ ยอดถอนไม่มีเพดาน. ตัวเลขเหล่านี้กำหนดภาระของระบบโดยตรง เพราะเมื่อ กำหนดขั้นต่ำต่ำ ระบบต้อง รองรับธุรกรรมจำนวนมากขนาดเล็ก และต้อง ตัดยอดและเติมเครดิตแบบทันที. หาก การยืนยันเครดิตใช้เวลานานเกินไม่กี่วินาที ผู้ใช้จะ กดซ้ำ ทำให้เกิด รายการซ้อน และ เพิ่มโหลดฝั่งเซิร์ฟเวอร์ทันที.
การเติมเงินด้วยการสแกน QR ตัดขั้นตอนการกรอกข้อมูลและการแนบสลิป. เมื่อผู้ใช้ สแกนคิวอาร์ ระบบจะรับสถานะธุรกรรมจากธนาคารผ่าน API. จากนั้น backend จะ ผูกธุรกรรมเข้ากับบัญชีผู้ใช้ และ เพิ่มเครดิตเข้า wallet. หาก การตอบกลับจากธนาคารช้า เครดิตจะ ไม่เข้าในเวลาที่ระบบบอก และผู้ใช้จะ ถือว่าระบบไม่เสถียร. ดังนั้น ตัวเลข 3 วินาที หมายถึงการเชื่อมต่อกับธนาคารต้อง ทำงานอัตโนมัติทั้งหมด ไม่ พึ่งการตรวจสอบด้วยคน.
การรองรับหลายธนาคาร เช่น KBank, Bangkok Bank, Krung Thai Bank, Krungsri, SCB, CIMB Thai รวมถึง ทรูมันนี่ วอลเล็ท ทำให้ระบบต้อง รับ callback หลายต้นทาง. แต่ละธนาคารมีรูปแบบข้อมูลและเวลาตอบสนองต่างกัน. หากไม่มี โมดูลแปลงข้อมูลให้เป็นมาตรฐานเดียว ระบบจะ ยืนยันยอดได้ช้า และจะเกิด ยอดค้างระบบ.
หมวดหมู่เกม ถูกแยกเป็น สล็อตออนไลน์, เกมสด, กีฬา และ ยิงปลา. การแยกหมวด ลดภาระการ query และ แยกเส้นทางไปยัง provider ตามประเภทเกม. เกมสล็อต มัก เชื่อมต่อผ่าน session API ส่วน คาสิโนสด ใช้ สตรีมแบบสด. หาก หลุดเซสชัน ผู้เล่นจะ ถูกตัดออกจากเกมทันที. ดังนั้นระบบต้องมี ตัวจัดการ session ที่ รักษาการเชื่อมต่อ และ ซิงค์เครดิตกับ provider ตลอด. หาก ซิงค์พลาด เครดิตผู้เล่นกับผลเกมจะ ไม่ตรงกัน.
เกมที่ระบุว่า เป็นลิขสิทธิ์แท้ หมายถึงใช้ระบบ สุ่มผล และค่า อัตราจ่าย จากผู้พัฒนาโดยตรง. ผลลัพธ์แต่ละรอบถูก คำนวณจากฝั่ง provider ไม่ใช่จากฝั่งเว็บ. หากไม่มี การเชื่อมต่อกับเซิร์ฟเวอร์ต้นทาง เว็บจะ รับผลเกมจริงไม่ได้ และ license จะถูกยกเลิกทันที. การมี การรับรอง จึง ผูกกับโครงสร้างการส่งข้อมูล ไม่ใช่ แค่คำบนหน้าเว็บ.
ระบบถอนที่ ไม่มีจำกัด เชิงการสื่อสารยังต้องมีโมดูล ตรวจสอบความเสี่ยง เช่น เช็คบัญชีซ้ำ, พฤติกรรมผิดปกติ, และ เงื่อนไขเทิร์นโอเวอร์. หากไม่มีการตรวจสอบเหล่านี้ ผู้ใช้สามารถ สร้างบัญชีหลายบัญชี เพื่อ เอาโบนัส และ ถอนเงินออกเร็ว.
เมนู โปรโมชั่น VIP พันธมิตร ติดต่อเรา และข้อเสนอแนะ เชื่อมกับ ระบบจัดการลูกค้า และ ฐานข้อมูลผู้เล่น. ส่วน Affiliate ใช้เก็บ โค้ดอ้างอิง เพื่อ คิดคอมมิชชั่น. หากไม่มีระบบนี้ จะ ติดตามแหล่งที่มาของผู้ใช้ไม่ได้. แบบฟอร์มฟีดแบ็ก ใช้เก็บ error จริงจากผู้ใช้. หากไม่มีข้อมูลนี้ ปัญหา ความหน่วง หรือ การใช้งาน จะ แก้ไม่ทัน.
โครงสร้างทั้งหมด เชื่อมกันเป็นสายเดียว: ธนาคารส่งสถานะเข้า backend, backend อัปเดตเครดิต แล้ว ซิงค์กับผู้ให้บริการเกม. หากส่วนใดส่วนหนึ่ง ช้า ผู้ใช้จะเห็นผลทันทีในรูปแบบ ยอดไม่เข้า, เกมค้าง หรือ ถอนช้า. ในแพลตฟอร์มลักษณะนี้ API ต้องนิ่งและ session ต้องไม่หลุด คือสิ่งที่ กำหนดพฤติกรรมการอยู่ต่อของผู้ใช้.
สล็อต
TKBNEKO เป็นแพลตฟอร์มเกมออนไลน์ ที่ วางระบบโดยยึดการใช้งานจริงของผู้เล่นเป็นแกนหลัก. หน้าแรก แสดงเงื่อนไขแบบเป็นตัวเลขตั้งแต่แรก: ขั้นต่ำฝาก 1 บาท, ถอนขั้นต่ำ 1 บาท, เครดิตเข้าโดยเฉลี่ยราว 3 วินาที, และ ไม่จำกัดยอดถอน. ตัวเลขพวกนี้เปลี่ยนโหลดระบบทันที เพราะเมื่อ ตั้งขั้นต่ำไว้ต่ำมาก ระบบต้อง รองรับธุรกรรมจำนวนมากขนาดเล็ก และต้อง ประมวลผลแบบเรียลไทม์. หาก เครดิตเข้าไม่ทันในไม่กี่วินาที ผู้ใช้จะ ทำรายการซ้ำ ทำให้เกิด รายการซ้อน และ เพิ่มโหลดฝั่งเซิร์ฟเวอร์ทันที.
การฝากผ่าน QR Code ตัดขั้นตอนการกรอกข้อมูลและการแนบสลิป. เมื่อผู้ใช้ สแกนคิวอาร์ ระบบจะรับสถานะธุรกรรมจากธนาคารผ่าน API. จากนั้น backend จะ จับคู่ธุรกรรมกับ user ID และ เพิ่มเครดิตเข้า wallet. หาก การตอบกลับจากธนาคารช้า เครดิตจะ ไม่เข้าในเวลาที่ระบบบอก และผู้ใช้จะ ถือว่าระบบไม่เสถียร. ดังนั้น ระยะเวลา 3 วินาที หมายถึงการเชื่อมต่อกับธนาคารต้อง เป็นแบบอัตโนมัติเต็มรูปแบบ ไม่ อาศัยแอดมินเช็คมือ.
การรองรับหลายธนาคาร เช่น KBank, Bangkok Bank, KTB, Krungsri, SCB, ซีไอเอ็มบี ไทย รวมถึง TrueMoney Wallet ทำให้ระบบต้อง จัดการ webhook หลายแหล่ง. แต่ละธนาคารมีรูปแบบข้อมูลและเวลาตอบสนองต่างกัน. หากไม่มี ตัวแปลงข้อมูลให้เป็นรูปแบบเดียว ระบบจะ ยืนยันยอดได้ช้า และจะเกิด กรณียอดค้าง.
หมวดหมู่เกม ถูกแยกเป็น สล็อตออนไลน์, เกมสด, กีฬา และ เกมยิงปลา. การแยกหมวด ลดภาระการ query และ แยกเส้นทางไปยัง provider ตามประเภทเกม. เกมสล็อต มัก ทำงานผ่าน session API ส่วน เกมสด ใช้ สตรีมภาพแบบเรียลไทม์. หาก หลุดเซสชัน ผู้เล่นจะ ถูกตัดออกจากเกมทันที. ดังนั้นระบบต้องมี ตัวจัดการ session ที่ รักษาการเชื่อมต่อ และ ซิงค์เครดิตกับ provider ภายนอกตลอดเวลา. หาก ซิงค์พลาด เครดิตผู้เล่นกับผลเกมจะ ไม่แมตช์.
เกมที่ระบุว่า เป็นลิขสิทธิ์แท้ หมายถึงใช้ระบบ สุ่มผล และค่า RTP จากผู้พัฒนาโดยตรง. ผลลัพธ์แต่ละรอบถูก ประมวลผลจากเซิร์ฟเวอร์ผู้ให้บริการ ไม่ใช่จากฝั่งเว็บ. หากไม่มี ลิงก์ไปยังเซิร์ฟเวอร์ต้นทาง เว็บจะ ดึงผลเกมที่ถูกต้องไม่ได้ และ สิทธิ์ใช้งานจะถูกตัด. การมี ใบรับรอง จึง ผูกกับโครงสร้างการส่งข้อมูล ไม่ใช่ แค่ข้อความแสดงบนหน้าเว็บ.
ระบบถอนที่ ไม่จำกัด เชิงการสื่อสารยังต้องมีโมดูล risk control เช่น เช็คบัญชีซ้ำ, พฤติกรรมผิดปกติ, และ เงื่อนไข turnover. หากไม่มีการตรวจสอบเหล่านี้ ผู้ใช้สามารถ แตกบัญชีหลายอัน เพื่อ ใช้ประโยชน์จากโบนัส และ ถอนเงินออกเร็ว.
ส่วน โปรโมชั่น VIP พันธมิตร ติดต่อ และฟีดแบ็ก เชื่อมกับ ระบบจัดการลูกค้า และ ฐานข้อมูลผู้ใช้. ส่วน พันธมิตร ใช้เก็บ referrer code เพื่อ คำนวณค่าคอมมิชชั่น. หากไม่มีระบบนี้ จะ track ที่มาผู้ใช้ไม่ได้. แบบฟอร์มฟีดแบ็ก ใช้เก็บ ข้อผิดพลาดจริงจากผู้ใช้. หากไม่มีข้อมูลนี้ ปัญหา ความหน่วง หรือ UX จะ แก้ไม่ทัน.
โครงสร้างทั้งหมด เชื่อมกันเป็นสายเดียว: สถานะธุรกรรมเข้ามาที่ backend, backend อัปเดตเครดิต แล้ว ซิงค์ไปยัง provider. หากส่วนใดส่วนหนึ่ง หน่วง ผู้ใช้จะเห็นผลทันทีในรูปแบบ ยอดไม่เข้า, เกมหน่วง หรือ ถอนช้า. ในแพลตฟอร์มลักษณะนี้ API ต้องนิ่งและ session ต้องไม่หลุด คือสิ่งที่ ตัดสินว่าผู้ใช้จะอยู่หรือย้ายออก.
pg slot แพลตฟอร์มเกมสล็อตยอดนิยม เล่นง่าย ฝากถอนเร็ว
คำค้นหา PG Slot กำลังได้รับความนิยมอย่างต่อเนื่อง ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น ผู้ให้บริการเกมสล็อตที่มาแรง ด้าน งานภาพคุณภาพสูง ความ เสถียร และ โอกาสรับกำไรที่ดี เกมของ PG ออกแบบโดยทีมงานมืออาชีพ ที่รองรับการเล่นทั้งบน สมาร์ทโฟน และ พีซี
ข้อดี ของ สล็อต PG
PG Slot เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ โหลดเร็ว เล่นผ่าน ระบบเว็บ และรองรับ ทั้ง iOS และ Android ไม่ต้องดาวน์โหลดแอป ผู้เล่นสามารถเข้าเล่นผ่าน Browser ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ เอฟเฟกต์ 3 มิติ ให้ความคมชัด พร้อมเอฟเฟกต์ จัดเต็ม
คุณสมบัติหลักของเกม สล็อต PG ได้แก่
ระบบโบนัสและฟรีสปินหลากหลายรูปแบบ
ระบบตัวคูณ
เล่นฟรีก่อนเติมเงิน
มีเมนูภาษาไทย
ระบบการเงินรวดเร็ว ไม่ต้องรอนาน
แพลตฟอร์ม สล็อต PG ส่วนใหญ่รองรับ การฝาก-ถอน ออโต้ตลอด 24 ชม. ขั้นต่ำเริ่มต้นเพียง 1 บาท ขึ้นอยู่กับ กติกาแต่ละแพลตฟอร์ม การทำรายการใช้เวลา รวดเร็วมาก ผ่าน สแกน QR หรือระบบ Mobile Banking ทำให้ธุรกรรมเป็นไปอย่าง ลื่นไหล
ประเภทเกมยอดนิยม ใน pg slot
เกม pg slot มีธีมหลากหลาย เช่น
ธีม แฟนตาซี
ธีม ลุยด่าน
ธีม โชคลาภ
ธีม ธรรมชาติ
ผู้เล่นนิยมเกมที่มีรอบพิเศษบ่อย พร้อมระบบ ฟีเจอร์พิเศษ และ โอกาสทำกำไรสูง เหมาะกับทั้ง ผู้เล่นเริ่มต้น และ สายสล็อตจริงจัง
ความน่าเชื่อถือ
สล็อต PG มีมาตรฐานรองรับ มีการ เข้ารหัสข้อมูล และใช้ระบบสุ่มผล ระบบสุ่มมาตรฐาน เพื่อให้ผลลัพธ์ ตรวจสอบได้ แพลตฟอร์มที่ให้บริการ PG Slot ควรมี ความปลอดภัยสูง
บทสรุปท้ายบท
สล็อต PG เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน โบนัสหลากหลาย และการทำธุรกรรมที่ รวดเร็ว ผู้เล่นสามารถเริ่มต้นได้ ง่าย ฝากถอนสะดวก และเลือกเกมได้ ครบทุกหมวด เหมาะสำหรับ ผู้เล่นทุกสไตล์ ในโลกของเกมสล็อตออนไลน์
สล็อต
แพลตฟอร์ม TKBNEKO เปิดประสบการณ์ใหม่แห่งการเดิมพันออนไลน์ ฝาก-ถอนไว ด้วยระบบสแกน คิวอาร์โค้ด
ในยุคดิจิทัลที่ โลกออนไลน์เติบโตต่อเนื่อง เรามุ่งเน้นมาตรฐานใหม่ของการเดิมพัน ด้วยระบบที่ ล้ำสมัย เสถียร และ ตรวจสอบได้ เพื่อให้ผู้เล่น อุ่นใจ ทุกครั้งที่ใช้งาน
ระบบการเงินที่ใช้งานง่าย
ฝากขั้นต่ำ: เริ่มต้น 1 บาท
ถอนขั้นต่ำ: 1 บาท
เวลาฝากเงิน: ภายใน 3 วินาที
ยอดถอน: ไม่จำกัดต่อวัน
เติมเงินง่าย แค่สแกน
สแกน QR Code ระบบจะ โอนเงินเข้าทันที ขั้นต่ำ เริ่ม 100 บาท สูงสุด ไม่เกิน 500,000 บาทต่อครั้ง
เกมยอดนิยม
สล็อต: ธีมหลากหลาย
เกมสด: ดีลเลอร์สด
กีฬา: แมตช์ทั่วโลก
ยิงปลา: สนุกได้เงินจริง
โบนัสและโปรโมชัน
ติดตามหน้า โปรโมชั่น พร้อมระบบ VIP และโปรแกรม แอฟฟิลิเอต
ติดต่อเรา
สอบถามข้อมูลได้ตลอด 24 ชั่วโมง ผ่านหน้า ติดต่อเรา ทีมงาน TKBNEKO พร้อมดูแลตลอดเวลา
PG Slot เกมสล็อตออนไลน์ที่คนค้นหาเยอะ เล่นง่าย ฝากถอนเร็ว
คำค้นหา pg slot กำลังได้รับความนิยมอย่างต่อเนื่อง ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น ค่ายเกมที่มีชื่อเสียง ด้าน กราฟิก ความ นิ่งไม่สะดุด และ อัตราการจ่ายรางวัลที่น่าสนใจ เกมของ PG ออกแบบโดยทีมงานมืออาชีพ ที่รองรับการเล่นทั้งบน มือถือ และ เดสก์ท็อป
ข้อดี ของ PG Slot
สล็อต PG เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ เปิดเกมได้ทันที เล่นผ่าน ระบบอัตโนมัติ และรองรับ ทุกอุปกรณ์ ไม่ต้องติดตั้งเพิ่มเติม ผู้เล่นสามารถเข้าเล่นผ่าน Browser ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ 3D ให้ความคมชัด พร้อมเอฟเฟกต์ จัดเต็ม
คุณสมบัติหลักของเกม PG Slot ได้แก่
โบนัสและฟรีสปินหลายแบบ
ฟีเจอร์ตัวคูณรางวัล
เดโม่ฟรี
ใช้งานภาษาไทยง่าย
ระบบฝากถอนสะดวก ทำรายการไว
แพลตฟอร์ม PG Slot ส่วนใหญ่รองรับ การฝาก-ถอน ออโต้ตลอด 24 ชม. ขั้นต่ำเริ่มต้นเพียง 10 บาท ขึ้นอยู่กับ เงื่อนไขของเว็บไซต์ การทำรายการใช้เวลา รวดเร็วมาก ผ่าน คิวอาร์โค้ด หรือระบบ Mobile Banking ทำให้ธุรกรรมเป็นไปอย่าง ต่อเนื่อง
ประเภทเกมยอดนิยม ใน PG Slot
เกม สล็อต PG มีธีมหลากหลาย เช่น
ธีม เทพเจ้าและแฟนตาซี
ธีม ผจญภัย
ธีม เอเชียและโชคลาภ
ธีม ธรรมชาติ
เกมยอดนิยมมักเป็นเกมที่แตกง่าย พร้อมระบบ โบนัสรอบพิเศษ และ โอกาสทำกำไรสูง เหมาะกับทั้ง มือใหม่ และ สายสล็อตจริงจัง
ความปลอดภัย
PG Slot พัฒนาในระบบสากล มีการ ปกป้องข้อมูลผู้เล่น และใช้ระบบสุ่มผล Random Number Generator เพื่อให้ผลลัพธ์ โปร่งใส แพลตฟอร์มที่ให้บริการ PG Slot ควรมี ทีมซัพพอร์ต 24 ชม.
โดยภาพรวม
สล็อต PG เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน โบนัสหลากหลาย และการทำธุรกรรมที่ ไว ผู้เล่นสามารถเริ่มต้นได้ ง่าย ฝากถอนสะดวก และเลือกเกมได้ หลากหลายแนว เหมาะสำหรับ ทั้งมือใหม่และมือโปร ในโลกของเกมสล็อตออนไลน์
ทดลองเล่นสล็อต PG Slot เกมสล็อตออนไลน์ที่คนค้นหาเยอะ เล่นง่าย ฝากถอนเร็ว
คำค้นหา pg slot ถูกค้นหามากขึ้นเรื่อยๆ ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น ผู้ให้บริการเกมสล็อตที่มาแรง ด้าน ภาพและเอฟเฟกต์ ความ เสถียร และ ระบบจ่ายที่ดึงดูด เกมของ PG ผลิตโดยค่ายมาตรฐาน ที่รองรับการเล่นทั้งบน สมาร์ทโฟน และ พีซี
ความโดดเด่น ของ PG Slot
สล็อต PG เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ โหลดเร็ว เล่นผ่าน ระบบอัตโนมัติ และรองรับ ทุกแพลตฟอร์ม เข้าเล่นผ่านเว็บได้เลย ผู้เล่นสามารถเข้าเล่นผ่าน เว็บเบราว์เซอร์ ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ เอฟเฟกต์ 3 มิติ ให้ความคมชัด พร้อมเอฟเฟกต์ สวยงาม
คุณสมบัติหลักของเกม PG Slot ได้แก่
มีรอบโบนัสให้ลุ้นบ่อย
ระบบตัวคูณ
เล่นฟรีก่อนเติมเงิน
รองรับภาษาไทยเต็มรูปแบบ
ฝากถอนง่าย ทันใจ
แพลตฟอร์ม สล็อต PG มักมี การฝาก-ถอน ออโต้ตลอด 24 ชม. ขั้นต่ำเริ่มต้นเพียง 1 บาท ขึ้นอยู่กับ กติกาแต่ละแพลตฟอร์ม การทำรายการใช้เวลา เพียงไม่กี่วินาที ผ่าน QR Code หรือระบบ แอปธนาคาร ทำให้ธุรกรรมเป็นไปอย่าง ต่อเนื่อง
แนวเกมที่คนเล่นเยอะ ใน PG Slot
เกม PG Slot มีธีมหลากหลาย เช่น
ธีม แฟนตาซี
ธีม ลุยด่าน
ธีม เอเชียและโชคลาภ
ธีม Animal
ผู้เล่นนิยมเกมที่มีรอบพิเศษบ่อย พร้อมระบบ โบนัสรอบพิเศษ และ โอกาสทำกำไรสูง เหมาะกับทั้ง มือใหม่ และ สายสล็อตจริงจัง
มาตรฐานระบบ
สล็อต PG ใช้ระบบที่ได้มาตรฐาน มีการ ปกป้องข้อมูลผู้เล่น และใช้ระบบสุ่มผล RNG เพื่อให้ผลลัพธ์ ตรวจสอบได้ แพลตฟอร์มที่ให้บริการ สล็อต PG ควรมี ความปลอดภัยสูง
บทสรุปท้ายบท
PG Slot เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน ระบบลื่นไหล และการทำธุรกรรมที่ ทันใจ ผู้เล่นสามารถเริ่มต้นได้ ง่าย ฝากถอนสะดวก และเลือกเกมได้ จำนวนมาก เหมาะสำหรับ ทุกระดับประสบการณ์ ในโลกของเกมสล็อตออนไลน์
PG
pg slot แพลตฟอร์มเกมสล็อตยอดนิยม เล่นง่าย ฝากถอนเร็ว
คำค้นหา สล็อต PG กำลังได้รับความนิยมอย่างต่อเนื่อง ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น แบรนด์เกมที่โดดเด่น ด้าน ภาพและเอฟเฟกต์ ความ เสถียร และ อัตราการจ่ายรางวัลที่น่าสนใจ เกมของ PG ผลิตโดยค่ายมาตรฐาน ที่รองรับการเล่นทั้งบน โทรศัพท์มือถือ และ เดสก์ท็อป
จุดเด่น ของ PG Slot
pg slot เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ เข้าเกมไว เล่นผ่าน ระบบออนไลน์ และรองรับ ทั้ง iOS และ Android ไม่ต้องติดตั้งเพิ่มเติม ผู้เล่นสามารถเข้าเล่นผ่าน หน้าเว็บ ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ 3D ให้ความคมชัด พร้อมเอฟเฟกต์ จัดเต็ม
คุณสมบัติหลักของเกม pg slot ได้แก่
มีรอบโบนัสให้ลุ้นบ่อย
ระบบตัวคูณ
เล่นฟรีก่อนเติมเงิน
มีเมนูภาษาไทย
ระบบฝากถอนสะดวก ไม่ต้องรอนาน
แพลตฟอร์ม PG Slot โดยทั่วไปให้บริการ การฝาก-ถอน ฝากถอนตลอดเวลา ขั้นต่ำเริ่มต้นเพียง หลักหน่วย ขึ้นอยู่กับ กติกาแต่ละแพลตฟอร์ม การทำรายการใช้เวลา รวดเร็วมาก ผ่าน สแกน QR หรือระบบ ธนาคารบนมือถือ ทำให้ธุรกรรมเป็นไปอย่าง ไม่สะดุด
ประเภทเกมยอดนิยม ใน PG Slot
เกม สล็อต PG มีธีมหลากหลาย เช่น
ธีม เทพเจ้าและแฟนตาซี
ธีม ผจญภัย
ธีม ความมั่งคั่ง
ธีม Animal
ผู้เล่นนิยมเกมที่มีรอบพิเศษบ่อย พร้อมระบบ Special Feature และ โอกาสทำกำไรสูง เหมาะกับทั้ง คนเพิ่งเล่น และ ผู้เล่นมือโปร
ความน่าเชื่อถือ
PG Slot ใช้ระบบที่ได้มาตรฐาน มีการ รักษาความปลอดภัย และใช้ระบบสุ่มผล RNG เพื่อให้ผลลัพธ์ ตรวจสอบได้ แพลตฟอร์มที่ให้บริการ pg slot ควรมี ระบบดูแลข้อมูล
บทสรุปท้ายบท
PG Slot เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน ระบบลื่นไหล และการทำธุรกรรมที่ ไว ผู้เล่นสามารถเริ่มต้นได้ ง่าย ฝากถอนสะดวก และเลือกเกมได้ ครบทุกหมวด เหมาะสำหรับ ทั้งมือใหม่และมือโปร ในโลกของเกมสล็อตออนไลน์
ทดลองเล่นสล็อต pg ซื้อฟรีสปิน
ทดลองเล่นสล็อต pg
TKBNEKO เปิดประสบการณ์ใหม่แห่งการเดิมพันออนไลน์ ฝาก-ถอนไว ด้วยระบบสแกน QR Code
ในยุคดิจิทัลที่ โลกออนไลน์เติบโตต่อเนื่อง TKBNEKO พร้อมยกระดับการให้บริการ ด้วยระบบที่ ล้ำสมัย เสถียร และ ตรวจสอบได้ เพื่อให้ผู้เล่น อุ่นใจ ทุกครั้งที่ใช้งาน
จุดเด่นระบบฝาก-ถอน
ฝากขั้นต่ำ: เริ่มต้น 1 บาท
ถอนขั้นต่ำ: ขั้นต่ำ 1 บาท
เวลาฝากเงิน: ภายใน 3 วินาที
ยอดถอน: ไม่มีลิมิต
เติมเงินง่าย แค่สแกน
สแกน QR Code ระบบจะ ประมวลผลอัตโนมัติ ขั้นต่ำ เริ่ม 100 บาท สูงสุด 500,000 บาท
เกมยอดนิยม
สล็อต: ธีมหลากหลาย
เกมสด: คาสิโนเรียลไทม์
กีฬา: แมตช์ทั่วโลก
ยิงปลา: สนุกได้เงินจริง
โปรโมชั่นและสิทธิพิเศษ
ติดตามหน้า โบนัส พร้อมระบบ VIP และโปรแกรม พันธมิตร
ฝ่ายบริการลูกค้า
สอบถามข้อมูลได้ตลอด 24 ชั่วโมง ผ่านหน้า ศูนย์ช่วยเหลือ ทีมงาน ของเรา พร้อมดูแลตลอดเวลา
скачать мелбет казино на андроид
Установить Melbet: Android, iPhone и ПК
Мобильная версия Melbet объединяет букмекерскую контору и казино в едином приложении. Пользователю доступны live-ставки, казино-игры, онлайн-трансляции, аналитика и операции по счёту. Установка занимает несколько минут.
Android (APK)
Загрузите APK с официального источника, запустите установщик и завершите установку. При необходимости включите доступ к установке сторонних приложений, затем войдите в аккаунт.
iOS (iPhone)
Перейдите в App Store, найдите «Melbet», нажмите «Получить», после установки авторизуйтесь в системе.
ПК
Откройте официальный сайт, авторизуйтесь и создайте ярлык на рабочий стол. Браузерная версия функционирует как отдельное приложение.
Функционал
Live-ставки с мгновенным обновлением линии, игровой раздел с тысячами игр, прямые трансляции, подробная статистика, push-оповещения, регистрация за минуту и поддержка 24/7.
Бонусы
После загрузки доступны бонус на первый депозит, акционные коды и фрибеты. Правила начисления определяются регионом.
Безопасность
Загружайте только с официальных источников, контролируйте адрес сайта, не передавайте пароль третьим лицам и активируйте двухфакторную аутентификацию.
Установка занимает несколько минут, после чего открывается полный доступ Melbet.
скачать приложение мелбет
Скачать приложение Melbet: Android, iPhone и ПК
Приложение Melbet включает букмекерскую контору и казино в едином приложении. Пользователю доступны live-ставки, слоты, прямые трансляции, статистика и операции по счёту. Установка занимает несколько минут.
Android (APK)
Загрузите APK с официального источника, откройте файл и подтвердите установку. При необходимости включите разрешение на установку из неизвестных источников, затем авторизуйтесь.
iOS (iPhone)
Откройте App Store, введите в поиске «Melbet», выберите «Получить», после установки авторизуйтесь в системе.
ПК
Откройте официальный сайт, авторизуйтесь и создайте ярлык на рабочий стол. Веб-версия работает как полноценное приложение.
Функционал
Live-ставки с мгновенным обновлением линии, казино и слоты, просмотр матчей, аналитические данные, уведомления о матчах, регистрация за минуту и поддержка 24/7.
Бонусы
После установки доступны приветственный бонус, акционные коды и бесплатные ставки. Условия зависят от региона.
Безопасность
Загружайте только с официального сайта, контролируйте адрес сайта, не сообщайте данные доступа третьим лицам и включите 2FA.
Загрузка выполняется быстро, после чего доступен весь функционал Melbet.
melbet официальный сайт скачать
Скачать приложение Melbet: Android, iPhone и ПК
Приложение Melbet объединяет букмекерскую контору и казино в одном интерфейсе. Доступны live-ставки, казино-игры, прямые трансляции, статистика и быстрые финансовые операции. Установка занимает 1–2 минуты.
Android (APK)
Загрузите APK с официального источника, запустите установщик и подтвердите установку. При необходимости включите разрешение на установку из неизвестных источников, затем авторизуйтесь.
iOS (iPhone)
Перейдите в App Store, введите в поиске «Melbet», нажмите «Получить», после установки выполните вход.
ПК
Откройте официальный сайт, авторизуйтесь и добавьте ярлык на рабочий стол. Браузерная версия функционирует как отдельное приложение.
Функционал
Live-ставки с обновлением коэффициентов, казино и слоты, прямые трансляции, подробная статистика, уведомления о матчах, быстрая регистрация и круглосуточная служба поддержки.
Бонусы
После загрузки доступны приветственный бонус, промокоды и бесплатные ставки. Условия зависят от региона.
Безопасность
Загружайте только с официальных источников, контролируйте адрес сайта, не передавайте пароль третьим лицам и включите 2FA.
Загрузка выполняется быстро, после чего открывается полный доступ Melbet.
мелбет вывод
Установить приложение Melbet: Android, iPhone и компьютер
Приложение Melbet включает букмекерскую контору и казино в едином приложении. Пользователю доступны live-ставки, казино-игры, прямые трансляции, аналитика и операции по счёту. Загрузка занимает 1–2 минуты.
Android (APK)
Скачайте APK с официального источника, запустите установщик и завершите установку. Если требуется включите разрешение на установку из неизвестных источников, затем войдите в аккаунт.
iOS (iPhone)
Откройте App Store, найдите «Melbet», выберите «Получить», после установки авторизуйтесь в системе.
ПК
Откройте официальный сайт, авторизуйтесь и создайте ярлык на рабочий стол. Браузерная версия функционирует как отдельное приложение.
Функционал
Live-ставки с мгновенным обновлением линии, игровой раздел с тысячами игр, просмотр матчей, подробная статистика, уведомления о матчах, быстрая регистрация и поддержка 24/7.
Бонусы
После загрузки доступны приветственный бонус, акционные коды и фрибеты. Правила начисления определяются регионом.
Безопасность
Скачивайте только с официального сайта, проверяйте домен, не передавайте пароль третьим лицам и активируйте двухфакторную аутентификацию.
Загрузка выполняется быстро, после чего доступен весь функционал Melbet.
melbet промокод
Установить приложение Melbet: APK, iPhone и компьютер
Приложение Melbet объединяет ставки и казино в одном интерфейсе. Доступны live-ставки, казино-игры, прямые трансляции, статистика и быстрые финансовые операции. Установка занимает 1–2 минуты.
Android (APK)
Скачайте APK с официального сайта, откройте файл и завершите установку. При необходимости включите доступ к установке сторонних приложений, затем войдите в аккаунт.
iOS (iPhone)
Откройте App Store, найдите «Melbet», нажмите «Получить», после установки выполните вход.
ПК
Откройте официальный сайт, авторизуйтесь и создайте ярлык на рабочий стол. Веб-версия работает как отдельное приложение.
Функционал
Live-ставки с мгновенным обновлением линии, игровой раздел с тысячами игр, прямые трансляции, аналитические данные, уведомления о матчах, быстрая регистрация и круглосуточная служба поддержки.
Бонусы
После загрузки доступны бонус на первый депозит, акционные коды и бесплатные ставки. Правила начисления определяются регионом.
Безопасность
Скачивайте только с официальных источников, контролируйте адрес сайта, не передавайте пароль третьим лицам и включите 2FA.
Установка занимает несколько минут, после чего открывается полный доступ Melbet.
pg
TKBNEKO พาคุณสู่โลกใหม่ของเกมเดิมพันออนไลน์ ธุรกรรมฉับไว ด้วยระบบสแกน QR Code
ในยุคที่ โลกออนไลน์พัฒนาอย่างรวดเร็ว TKBNEKO พร้อมยกระดับมาตรฐานการเดิมพัน ด้วยระบบการให้บริการที่ ทันสมัย เสถียร และ ตรวจสอบได้ พร้อมต้อนรับสมาชิกทุกท่านสู่ โลกแห่งเกมที่เหนือกว่าเดิม ที่ ตอบโจทย์ทั้งมือใหม่และมืออาชีพ
เหตุผลที่ควรเลือก TKBNEKO
เราคัดสรรเกมคุณภาพจากผู้พัฒนาชั้นนำ โดยเฉพาะเกมที่ มีใบรับรองอย่างถูกต้อง และ ได้มาตรฐานสากล เพื่อให้ผู้เล่นทุกคน อุ่นใจ ได้ว่า จะได้รับความเพลิดเพลินกับเกมที่ ยุติธรรม มีระบบรักษาความปลอดภัยสูง และ ตอบโจทย์ผู้เล่นยุคใหม่
จุดเด่นของระบบฝาก-ถอน
เราออกแบบระบบการเงินให้ง่ายและเร็วที่สุด เพื่อให้คุณ เล่นเกมได้แบบไม่สะดุด
ฝากขั้นต่ำ: ขั้นต่ำแค่ 1 บาท
ถอนขั้นต่ำ: เพียง 1 บาท
เวลาฝากเงิน: รวดเร็วทันใจใน 3 วินาที
ยอดจำกัดการถอน: ไม่มีลิมิตการถอนรายวัน
เติมเงินง่ายด้วย QR Code
เพียงคุณสแกน คิวอาร์ ระบบของเราจะ ประมวลผลอย่างรวดเร็ว ขั้นต่ำเพียง 100 บาท และสามารถฝากได้สูงถึง ไม่เกิน 500,000 บาทต่อครั้ง เริ่มต้นได้ทันที กับ TKBNEKO ที่ ตอบโจทย์การเดิมพันยุคใหม่
เกมยอดนิยมรวมไว้ในที่เดียว
แพลตฟอร์มของเราครอบคลุมทุกแนวเกม รองรับทุกความชอบของผู้เล่น
สล็อต: หลากหลายธีม แจ็คพอตรอคุณอยู่
เกมสด: สัมผัสประสบการณ์คาสิโนแบบเรียลไทม์
กีฬา: วางเดิมพันกีฬาหลากหลายรายการ
ยิงปลา: เกมยิงปลาสุดมันส์ ได้เงินจริง
อัปเดตโปรโมชันล่าสุด
อย่าลืมแวะมาเยี่ยมชมที่หน้า โปรโมชันล่าสุด เพื่อรับ ของรางวัลพิเศษ ที่เรามอบให้สมาชิกทุกท่าน นอกจากนี้ยังมีระบบ VIP สำหรับลูกค้าคนสำคัญ และช่องทาง พาร์ทเนอร์ สำหรับผู้ที่สนใจสร้างรายได้ร่วมกับเรา
ช่องทางติดต่อ
หากมี ข้อสงสัย หรือ คำแนะนำ สามารถติดต่อทีมงานของเราได้ตลอด 24 ชั่วโมงที่หน้า ติดต่อเรา และ แบบฟอร์มติดต่อ ทีมงาน TKBNEKO ยินดีให้บริการทุกท่านด้วยใจ
PG Slot เกมสล็อตออนไลน์ที่คนค้นหาเยอะ เล่นง่าย ฝากถอนเร็ว
คำค้นหา สล็อต PG มาแรงในช่วงนี้ ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น แบรนด์เกมที่โดดเด่น ด้าน ภาพและเอฟเฟกต์ ความ นิ่งไม่สะดุด และ โอกาสรับกำไรที่ดี เกมของ PG ผลิตโดยค่ายมาตรฐาน ที่รองรับการเล่นทั้งบน โทรศัพท์มือถือ และ เดสก์ท็อป
จุดเด่น ของ สล็อต PG
สล็อต PG เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ โหลดเร็ว เล่นผ่าน ระบบอัตโนมัติ และรองรับ ทุกอุปกรณ์ เข้าเล่นผ่านเว็บได้เลย ผู้เล่นสามารถเข้าเล่นผ่าน Browser ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ 3D ให้ความคมชัด พร้อมเอฟเฟกต์ จัดเต็ม
คุณสมบัติหลักของเกม สล็อต PG ได้แก่
โบนัสและฟรีสปินหลายแบบ
Multiplier
เล่นฟรีก่อนเติมเงิน
มีเมนูภาษาไทย
ระบบการเงินรวดเร็ว ทำรายการไว
แพลตฟอร์ม pg slot มักมี การฝาก-ถอน ฝากถอนตลอดเวลา ขั้นต่ำเริ่มต้นเพียง หลักหน่วย ขึ้นอยู่กับ เงื่อนไขของเว็บไซต์ การทำรายการใช้เวลา เพียงไม่กี่วินาที ผ่าน คิวอาร์โค้ด หรือระบบ Mobile Banking ทำให้ธุรกรรมเป็นไปอย่าง ไม่สะดุด
หมวดเกมฮิต ใน pg slot
เกม pg slot มีธีมหลากหลาย เช่น
ธีม เทพเจ้า
ธีม ผจญภัย
ธีม โชคลาภ
ธีม Animal
ผู้เล่นนิยมเกมที่มีรอบพิเศษบ่อย พร้อมระบบ ฟีเจอร์พิเศษ และ โอกาสทำกำไรสูง เหมาะกับทั้ง มือใหม่ และ สายสล็อตจริงจัง
ความปลอดภัย
PG Slot พัฒนาในระบบสากล มีการ รักษาความปลอดภัย และใช้ระบบสุ่มผล Random Number Generator เพื่อให้ผลลัพธ์ ตรวจสอบได้ แพลตฟอร์มที่ให้บริการ pg slot ควรมี ระบบดูแลข้อมูล
โดยภาพรวม
สล็อต PG เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน กราฟิกคุณภาพ และการทำธุรกรรมที่ ทันใจ ผู้เล่นสามารถเริ่มต้นได้ ทันที ฝากถอนสะดวก และเลือกเกมได้ ครบทุกหมวด เหมาะสำหรับ ทั้งมือใหม่และมือโปร ในโลกของเกมสล็อตออนไลน์
สล็อต
TKBNEKO มอบมิติใหม่ของเกมออนไลน์ ธุรกรรมรวดเร็ว ด้วยระบบสแกน คิวอาร์โค้ด
ในยุคดิจิทัลที่ โลกออนไลน์เติบโตต่อเนื่อง เรามุ่งเน้นมาตรฐานใหม่ของการเดิมพัน ด้วยระบบที่ ทันสมัย รวดเร็ว และ โปร่งใส เพื่อให้ผู้เล่น มั่นใจ ทุกครั้งที่ใช้งาน
จุดเด่นระบบฝาก-ถอน
ฝากขั้นต่ำ: 1 บาท
ถอนขั้นต่ำ: ขั้นต่ำ 1 บาท
เวลาฝากเงิน: ใช้เวลาเพียง 3 วินาที
ยอดถอน: ไม่มีลิมิต
ฝากง่าย เพียงสแกน QR Code
สแกน QR Code ระบบจะ โอนเงินเข้าทันที ขั้นต่ำ 100 บาท สูงสุด 500,000 บาท
เกมยอดนิยม
สล็อต: ธีมหลากหลาย
เกมสด: คาสิโนเรียลไทม์
กีฬา: เดิมพันลีกดัง
ยิงปลา: ลุ้นกำไรทันที
โปรโมชั่นและสิทธิพิเศษ
ติดตามหน้า โบนัส พร้อมระบบ VIP และโปรแกรม พันธมิตร
ฝ่ายบริการลูกค้า
สอบถามข้อมูลได้ตลอด 24 ชั่วโมง ผ่านหน้า ติดต่อเรา ทีมงาน ของเรา พร้อมดูแลตลอดเวลา
ทดลองเล่นสล็อต pg ฟรี PG Slot สล็อตยอดฮิต เล่นง่าย ฝากถอนเร็ว
คำค้นหา สล็อต PG มาแรงในช่วงนี้ ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น ผู้ให้บริการเกมสล็อตที่มาแรง ด้าน งานภาพคุณภาพสูง ความ นิ่งไม่สะดุด และ ระบบจ่ายที่ดึงดูด เกมของ PG ผลิตโดยค่ายมาตรฐาน ที่รองรับการเล่นทั้งบน โทรศัพท์มือถือ และ พีซี
ข้อดี ของ สล็อต PG
pg slot เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ เข้าเกมไว เล่นผ่าน ระบบเว็บ และรองรับ ทุกแพลตฟอร์ม ไม่ต้องติดตั้งเพิ่มเติม ผู้เล่นสามารถเข้าเล่นผ่าน เว็บเบราว์เซอร์ ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ สามมิติ ให้ความคมชัด พร้อมเอฟเฟกต์ สมจริง
คุณสมบัติหลักของเกม pg slot ได้แก่
โบนัสและฟรีสปินหลายแบบ
ระบบตัวคูณ
โหมดทดลองเล่นฟรี
รองรับภาษาไทยเต็มรูปแบบ
ระบบการเงินรวดเร็ว ทำรายการไว
แพลตฟอร์ม PG Slot ส่วนใหญ่รองรับ การฝาก-ถอน ฝากถอนตลอดเวลา ขั้นต่ำเริ่มต้นเพียง 1 บาท ขึ้นอยู่กับ กติกาแต่ละแพลตฟอร์ม การทำรายการใช้เวลา เพียงไม่กี่วินาที ผ่าน สแกน QR หรือระบบ ธนาคารบนมือถือ ทำให้ธุรกรรมเป็นไปอย่าง ลื่นไหล
หมวดเกมฮิต ใน pg slot
เกม pg slot มีธีมหลากหลาย เช่น
ธีม แฟนตาซี
ธีม ลุยด่าน
ธีม เอเชียและโชคลาภ
ธีม Animal
ผู้เล่นนิยมเกมที่มีรอบพิเศษบ่อย พร้อมระบบ ฟีเจอร์พิเศษ และ โอกาสทำกำไรสูง เหมาะกับทั้ง คนเพิ่งเล่น และ ผู้เล่นที่มีประสบการณ์
มาตรฐานระบบ
pg slot พัฒนาในระบบสากล มีการ รักษาความปลอดภัย และใช้ระบบสุ่มผล RNG เพื่อให้ผลลัพธ์ ยุติธรรม แพลตฟอร์มที่ให้บริการ สล็อต PG ควรมี ความปลอดภัยสูง
โดยภาพรวม
PG Slot เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน ระบบลื่นไหล และการทำธุรกรรมที่ ไว ผู้เล่นสามารถเริ่มต้นได้ ทันที ฝากถอนสะดวก และเลือกเกมได้ หลากหลายแนว เหมาะสำหรับ ทุกระดับประสบการณ์ ในโลกของเกมสล็อตออนไลน์
PG Slot เกมสล็อตออนไลน์ที่คนค้นหาเยอะ ใช้งานง่าย ฝากถอนรวดเร็ว
คำค้นหา สล็อต PG มาแรงในช่วงนี้ ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น ผู้ให้บริการเกมสล็อตที่มาแรง ด้าน งานภาพคุณภาพสูง ความ เสถียร และ โอกาสรับกำไรที่ดี เกมของ PG พัฒนาโดยผู้ให้บริการชั้นนำ ที่รองรับการเล่นทั้งบน โทรศัพท์มือถือ และ พีซี
ความโดดเด่น ของ PG Slot
pg slot เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ โหลดเร็ว เล่นผ่าน ระบบเว็บ และรองรับ ทั้ง iOS และ Android ไม่ต้องติดตั้งเพิ่มเติม ผู้เล่นสามารถเข้าเล่นผ่าน เว็บเบราว์เซอร์ ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ เอฟเฟกต์ 3 มิติ ให้ความคมชัด พร้อมเอฟเฟกต์ จัดเต็ม
คุณสมบัติหลักของเกม PG Slot ได้แก่
ระบบโบนัสและฟรีสปินหลากหลายรูปแบบ
ฟีเจอร์ตัวคูณรางวัล
เล่นฟรีก่อนเติมเงิน
ใช้งานภาษาไทยง่าย
ระบบฝากถอนสะดวก ทันใจ
แพลตฟอร์ม สล็อต PG มักมี การฝาก-ถอน ออโต้ตลอด 24 ชม. ขั้นต่ำเริ่มต้นเพียง หลักหน่วย ขึ้นอยู่กับ ระบบของผู้ให้บริการ การทำรายการใช้เวลา ไม่กี่วินาที ผ่าน คิวอาร์โค้ด หรือระบบ ธนาคารบนมือถือ ทำให้ธุรกรรมเป็นไปอย่าง ลื่นไหล
หมวดเกมฮิต ใน PG Slot
เกม PG Slot มีธีมหลากหลาย เช่น
ธีม เทพเจ้า
ธีม ลุยด่าน
ธีม โชคลาภ
ธีม Animal
เกมยอดนิยมมักเป็นเกมที่แตกง่าย พร้อมระบบ โบนัสรอบพิเศษ และ อัตราการจ่ายที่สูง เหมาะกับทั้ง ผู้เล่นเริ่มต้น และ ผู้เล่นที่มีประสบการณ์
มาตรฐานระบบ
PG Slot ใช้ระบบที่ได้มาตรฐาน มีการ รักษาความปลอดภัย และใช้ระบบสุ่มผล Random Number Generator เพื่อให้ผลลัพธ์ ตรวจสอบได้ แพลตฟอร์มที่ให้บริการ สล็อต PG ควรมี ระบบดูแลข้อมูล
โดยภาพรวม
pg slot เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน ระบบลื่นไหล และการทำธุรกรรมที่ ไว ผู้เล่นสามารถเริ่มต้นได้ ไม่ซับซ้อน ฝากถอนสะดวก และเลือกเกมได้ หลากหลายแนว เหมาะสำหรับ ทั้งมือใหม่และมือโปร ในโลกของเกมสล็อตออนไลน์
https://medium.com/@ratypw/ทดลองเล่นสล็อต-pg-70cdb1132344
ทดลองเล่นสล็อต pg ไม่ เด้ง
pg
เว็บไซต์ TKBNEKO พาคุณสู่โลกใหม่ของเกมเดิมพันออนไลน์ ฝาก-ถอนไว ด้วยระบบสแกน QR Code
ในยุคที่ นวัตกรรมดิจิทัลเข้ามาปรับโฉมวงการเกมออนไลน์ TKBNEKO ขอเป็นส่วนหนึ่งในการปฏิวัติวงการเกม ด้วยระบบการให้บริการที่ อัปเดตตลอดเวลา เสถียร และ ชัดเจน พร้อมต้อนรับสมาชิกทุกท่านสู่ โลกแห่งเกมที่เหนือกว่าเดิม ที่ ใครๆ ก็เป็นเถ้าแก่ได้
เพราะอะไรหลายคนจึงเลือก TKBNEKO
TKBNEKO มุ่งมั่นที่จะมอบประสบการณ์จากเกมลิขสิทธิ์แท้ โดยเฉพาะเกมที่ ผ่านการรับรองจากสถาบันที่น่าเชื่อถือ และ ได้มาตรฐานสากล เพื่อให้ผู้เล่นทุกคน อุ่นใจ ได้ว่า จะได้รับความเพลิดเพลินกับเกมที่ โปร่งใส ข้อมูลไม่รั่วไหล และ มีคุณภาพสูง
จุดเด่นของระบบฝาก-ถอน
เรามุ่งเน้นความสะดวกของผู้เล่น เพื่อให้คุณ โฟกัสกับความสนุกได้อย่างเต็มที่
ฝากขั้นต่ำ: ขั้นต่ำแค่ 1 บาท
ถอนขั้นต่ำ: ขั้นต่ำ 1 บาท
เวลาฝากเงิน: เงินเข้าภายใน 3 วินาที
ยอดจำกัดการถอน: ถอนได้ไม่จำกัดยอด
เติมเงินง่ายด้วย QR Code
เพียงคุณสแกน คิวอาร์ ระบบของเราจะ ประมวลผลอย่างรวดเร็ว ขั้นต่ำเพียง เริ่มต้น 100 บาท และสามารถฝากได้สูงถึง ไม่เกิน 500,000 บาทต่อครั้ง เริ่มต้นได้ทันที กับ TKBNEKO ที่ ใช้งานง่าย ทำกำไรได้รวดเร็ว
หมวดหมู่เกมที่ครบครัน
แพลตฟอร์มของเราครอบคลุมทุกแนวเกม รองรับทุกความชอบของผู้เล่น
สล็อต: หลากหลายธีม แจ็คพอตรอคุณอยู่
เกมสด: สัมผัสประสบการณ์คาสิโนแบบเรียลไทม์
กีฬา: รองรับลีกดังระดับโลก
ยิงปลา: ลุ้นกำไรจากเกมยิงปลา
อัปเดตโปรโมชันล่าสุด
อย่าลืมแวะมาเยี่ยมชมที่หน้า โบนัส เพื่อรับ ของรางวัลพิเศษ ที่เรามอบให้สมาชิกทุกท่าน นอกจากนี้ยังมีระบบ VIP สำหรับลูกค้าคนสำคัญ และช่องทาง แอฟฟิลิเอต สำหรับผู้ที่สนใจสร้างรายได้ร่วมกับเรา
ติดต่อเรา
หากมี ข้อสงสัย หรือ ความคิดเห็น สามารถติดต่อทีมงานของเราได้ตลอด 24 ชั่วโมงที่หน้า ฝ่ายสนับสนุน และ ส่งความคิดเห็น ทีมงาน ของเรา ยินดีให้บริการทุกท่านด้วยใจ
PG Slot แพลตฟอร์มเกมสล็อตยอดนิยม เข้าเล่นไว ฝากถอนออโต้
คำค้นหา สล็อต PG มาแรงในช่วงนี้ ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น ผู้ให้บริการเกมสล็อตที่มาแรง ด้าน ภาพและเอฟเฟกต์ ความ ลื่นไหล และ ระบบจ่ายที่ดึงดูด เกมของ PG พัฒนาโดยผู้ให้บริการชั้นนำ ที่รองรับการเล่นทั้งบน สมาร์ทโฟน และ เดสก์ท็อป
จุดเด่น ของ PG Slot
pg slot เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ โหลดเร็ว เล่นผ่าน ระบบออนไลน์ และรองรับ ทั้ง iOS และ Android เข้าเล่นผ่านเว็บได้เลย ผู้เล่นสามารถเข้าเล่นผ่าน หน้าเว็บ ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ สามมิติ ให้ความคมชัด พร้อมเอฟเฟกต์ สวยงาม
คุณสมบัติหลักของเกม PG Slot ได้แก่
มีรอบโบนัสให้ลุ้นบ่อย
Multiplier
เล่นฟรีก่อนเติมเงิน
ใช้งานภาษาไทยง่าย
ฝากถอนง่าย ไม่ต้องรอนาน
แพลตฟอร์ม สล็อต PG โดยทั่วไปให้บริการ การฝาก-ถอน อัตโนมัติ 24 ชั่วโมง ขั้นต่ำเริ่มต้นเพียง 10 บาท ขึ้นอยู่กับ เงื่อนไขของเว็บไซต์ การทำรายการใช้เวลา เพียงไม่กี่วินาที ผ่าน QR Code หรือระบบ Mobile Banking ทำให้ธุรกรรมเป็นไปอย่าง ต่อเนื่อง
ประเภทเกมยอดนิยม ใน PG Slot
เกม pg slot มีธีมหลากหลาย เช่น
ธีม เทพเจ้า
ธีม ลุยด่าน
ธีม ความมั่งคั่ง
ธีม สัตว์และธรรมชาติ
เกมยอดนิยมมักเป็นเกมที่แตกง่าย พร้อมระบบ โบนัสรอบพิเศษ และ อัตราการจ่ายที่สูง เหมาะกับทั้ง ผู้เล่นเริ่มต้น และ ผู้เล่นมือโปร
ความน่าเชื่อถือ
pg slot มีมาตรฐานรองรับ มีการ เข้ารหัสข้อมูล และใช้ระบบสุ่มผล RNG เพื่อให้ผลลัพธ์ โปร่งใส แพลตฟอร์มที่ให้บริการ pg slot ควรมี ทีมซัพพอร์ต 24 ชม.
โดยภาพรวม
สล็อต PG เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน โบนัสหลากหลาย และการทำธุรกรรมที่ รวดเร็ว ผู้เล่นสามารถเริ่มต้นได้ ทันที ฝากถอนสะดวก และเลือกเกมได้ ครบทุกหมวด เหมาะสำหรับ ทั้งมือใหม่และมือโปร ในโลกของเกมสล็อตออนไลน์
สล็อต
TKBNEKO เปิดประสบการณ์ใหม่แห่งการเดิมพันออนไลน์ ธุรกรรมรวดเร็ว ด้วยระบบสแกน คิวอาร์โค้ด
ในยุคดิจิทัลที่ โลกออนไลน์เติบโตต่อเนื่อง TKBNEKO พร้อมยกระดับการให้บริการ ด้วยระบบที่ ล้ำสมัย เสถียร และ โปร่งใส เพื่อให้ผู้เล่น มั่นใจ ทุกครั้งที่ใช้งาน
จุดเด่นระบบฝาก-ถอน
ฝากขั้นต่ำ: เริ่มต้น 1 บาท
ถอนขั้นต่ำ: ขั้นต่ำ 1 บาท
เวลาฝากเงิน: ใช้เวลาเพียง 3 วินาที
ยอดถอน: ไม่จำกัดต่อวัน
เติมเงินง่าย แค่สแกน
สแกน คิวอาร์ ระบบจะ โอนเงินเข้าทันที ขั้นต่ำ เริ่ม 100 บาท สูงสุด 500,000 บาท
เกมยอดนิยม
สล็อต: ลุ้นแจ็คพอต
เกมสด: ดีลเลอร์สด
กีฬา: แมตช์ทั่วโลก
ยิงปลา: ลุ้นกำไรทันที
โบนัสและโปรโมชัน
ติดตามหน้า โบนัส พร้อมระบบ VIP และโปรแกรม แอฟฟิลิเอต
ฝ่ายบริการลูกค้า
สอบถามข้อมูลได้ตลอด 24 ชั่วโมง ผ่านหน้า ศูนย์ช่วยเหลือ ทีมงาน TKBNEKO พร้อมดูแลตลอดเวลา
pg
TKBNEKO มอบมิติใหม่ของการเดิมพันออนไลน์ ฝาก-ถอนไว ด้วยระบบสแกน คิวอาร์โค้ด
ในยุคที่ โลกออนไลน์พัฒนาอย่างรวดเร็ว TKBNEKO พร้อมยกระดับมาตรฐานการเดิมพัน ด้วยระบบการให้บริการที่ ล้ำสมัย รวดเร็ว และ ชัดเจน พร้อมต้อนรับสมาชิกทุกท่านสู่ มิติใหม่แห่งความสนุก ที่ ใครๆ ก็เป็นเถ้าแก่ได้
ทำไมต้อง TKBNEKO?
เราคัดสรรเกมคุณภาพจากผู้พัฒนาชั้นนำ โดยเฉพาะเกมที่ ผ่านการรับรองจากสถาบันที่น่าเชื่อถือ และ เป็นที่นิยมในระดับสากล เพื่อให้ผู้เล่นทุกคน อุ่นใจ ได้ว่า จะได้รับความเพลิดเพลินกับเกมที่ โปร่งใส ข้อมูลไม่รั่วไหล และ ได้มาตรฐานระดับสากล
ระบบการเงินที่เหนือกว่า
เราออกแบบระบบการเงินให้ง่ายและเร็วที่สุด เพื่อให้คุณ โฟกัสกับความสนุกได้อย่างเต็มที่
ฝากขั้นต่ำ: เริ่มต้นเพียง 1 บาท
ถอนขั้นต่ำ: 1 บาท
เวลาฝากเงิน: ใช้เวลาเพียง 3 วินาที
ยอดจำกัดการถอน: ถอนได้ไม่จำกัดยอด
ธุรกรรมสะดวก แค่สแกนคิวอาร์
เพียงคุณสแกน QR Code ระบบของเราจะ ประมวลผลอย่างรวดเร็ว ขั้นต่ำเพียง อย่างน้อย 100 บาท และสามารถฝากได้สูงถึง สูงสุด 500,000 บาท เข้าร่วมความสนุกได้เลย กับ แพลตฟอร์มของเรา ที่ ใช้งานง่าย ทำกำไรได้รวดเร็ว
คลังเกมคุณภาพ
แพลตฟอร์มของเราครอบคลุมทุกแนวเกม รองรับทุกความชอบของผู้เล่น
สล็อต: ธีมมากมาย พร้อมลุ้นรางวัลใหญ่
เกมสด: ดีลเลอร์ถ่ายทอดสดตลอดเวลา
กีฬา: รองรับลีกดังระดับโลก
ยิงปลา: เกมยิงปลาสุดมันส์ ได้เงินจริง
ติดตามโปรโมชั่นและสิทธิพิเศษ
อย่าลืมแวะมาเยี่ยมชมที่หน้า โปรโมชันล่าสุด เพื่อรับ ของรางวัลพิเศษ ที่เรามอบให้สมาชิกทุกท่าน นอกจากนี้ยังมีระบบ ลูกค้าระดับพรีเมียม สำหรับลูกค้าคนสำคัญ และช่องทาง พันธมิตร สำหรับผู้ที่สนใจสร้างรายได้ร่วมกับเรา
ติดต่อเรา
หากมี คำถาม หรือ ความคิดเห็น สามารถติดต่อทีมงานของเราได้ตลอด 24 ชั่วโมงที่หน้า ศูนย์ช่วยเหลือ และ ส่งความคิดเห็น ทีมงาน ของเรา ยินดีให้บริการทุกท่านด้วยใจ
ทดลองเล่นสล็อต pg ฟรี สล็อต PG เกมสล็อตออนไลน์ที่คนค้นหาเยอะ ใช้งานง่าย ฝากถอนรวดเร็ว
คำค้นหา PG Slot กำลังได้รับความนิยมอย่างต่อเนื่อง ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น แบรนด์เกมที่โดดเด่น ด้าน กราฟิก ความ เสถียร และ ระบบจ่ายที่ดึงดูด เกมของ PG ออกแบบโดยทีมงานมืออาชีพ ที่รองรับการเล่นทั้งบน โทรศัพท์มือถือ และ พีซี
จุดเด่น ของ สล็อต PG
สล็อต PG เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ เข้าเกมไว เล่นผ่าน ระบบเว็บ และรองรับ ทุกแพลตฟอร์ม เข้าเล่นผ่านเว็บได้เลย ผู้เล่นสามารถเข้าเล่นผ่าน Browser ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ เอฟเฟกต์ 3 มิติ ให้ความคมชัด พร้อมเอฟเฟกต์ สมจริง
คุณสมบัติหลักของเกม PG Slot ได้แก่
มีรอบโบนัสให้ลุ้นบ่อย
ระบบตัวคูณ
เดโม่ฟรี
มีเมนูภาษาไทย
ฝากถอนง่าย ไม่ต้องรอนาน
แพลตฟอร์ม PG Slot ส่วนใหญ่รองรับ การฝาก-ถอน ออโต้ตลอด 24 ชม. ขั้นต่ำเริ่มต้นเพียง หลักหน่วย ขึ้นอยู่กับ ระบบของผู้ให้บริการ การทำรายการใช้เวลา รวดเร็วมาก ผ่าน สแกน QR หรือระบบ แอปธนาคาร ทำให้ธุรกรรมเป็นไปอย่าง ไม่สะดุด
หมวดเกมฮิต ใน pg slot
เกม PG Slot มีธีมหลากหลาย เช่น
ธีม เทพเจ้า
ธีม ลุยด่าน
ธีม ความมั่งคั่ง
ธีม สัตว์และธรรมชาติ
หลายคนชอบเกมที่โบนัสเข้าไว พร้อมระบบ โบนัสรอบพิเศษ และ อัตราการจ่ายที่สูง เหมาะกับทั้ง คนเพิ่งเล่น และ สายสล็อตจริงจัง
ความปลอดภัย
สล็อต PG พัฒนาในระบบสากล มีการ ปกป้องข้อมูลผู้เล่น และใช้ระบบสุ่มผล Random Number Generator เพื่อให้ผลลัพธ์ ตรวจสอบได้ แพลตฟอร์มที่ให้บริการ pg slot ควรมี ระบบดูแลข้อมูล
บทสรุปท้ายบท
pg slot เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน กราฟิกคุณภาพ และการทำธุรกรรมที่ รวดเร็ว ผู้เล่นสามารถเริ่มต้นได้ ทันที ฝากถอนสะดวก และเลือกเกมได้ จำนวนมาก เหมาะสำหรับ ทั้งมือใหม่และมือโปร ในโลกของเกมสล็อตออนไลน์
tuan88
ทดลองเล่นสล็อต pg เว็บ ตรง”
PG Slot แพลตฟอร์มเกมสล็อตยอดนิยม เข้าเล่นไว ฝากถอนออโต้
คำค้นหา สล็อต PG มาแรงในช่วงนี้ ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น แบรนด์เกมที่โดดเด่น ด้าน ภาพและเอฟเฟกต์ ความ เสถียร และ อัตราการจ่ายรางวัลที่น่าสนใจ เกมของ PG พัฒนาโดยผู้ให้บริการชั้นนำ ที่รองรับการเล่นทั้งบน มือถือ และ เดสก์ท็อป
ความโดดเด่น ของ PG Slot
PG Slot เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ เปิดเกมได้ทันที เล่นผ่าน ระบบอัตโนมัติ และรองรับ ทั้ง iOS และ Android ไม่ต้องติดตั้งเพิ่มเติม ผู้เล่นสามารถเข้าเล่นผ่าน เว็บเบราว์เซอร์ ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ สามมิติ ให้ความคมชัด พร้อมเอฟเฟกต์ จัดเต็ม
คุณสมบัติหลักของเกม PG Slot ได้แก่
โบนัสและฟรีสปินหลายแบบ
ฟีเจอร์ตัวคูณรางวัล
โหมดทดลองเล่นฟรี
ใช้งานภาษาไทยง่าย
ระบบการเงินรวดเร็ว ไม่ต้องรอนาน
แพลตฟอร์ม PG Slot โดยทั่วไปให้บริการ การฝาก-ถอน ฝากถอนตลอดเวลา ขั้นต่ำเริ่มต้นเพียง 1 บาท ขึ้นอยู่กับ เงื่อนไขของเว็บไซต์ การทำรายการใช้เวลา รวดเร็วมาก ผ่าน QR Code หรือระบบ ธนาคารบนมือถือ ทำให้ธุรกรรมเป็นไปอย่าง ไม่สะดุด
ประเภทเกมยอดนิยม ใน pg slot
เกม สล็อต PG มีธีมหลากหลาย เช่น
ธีม เทพเจ้าและแฟนตาซี
ธีม Adventure
ธีม เอเชียและโชคลาภ
ธีม ธรรมชาติ
ผู้เล่นนิยมเกมที่มีรอบพิเศษบ่อย พร้อมระบบ ฟีเจอร์พิเศษ และ ระบบจ่ายคุ้มค่า เหมาะกับทั้ง คนเพิ่งเล่น และ สายสล็อตจริงจัง
ความปลอดภัย
pg slot พัฒนาในระบบสากล มีการ ปกป้องข้อมูลผู้เล่น และใช้ระบบสุ่มผล RNG เพื่อให้ผลลัพธ์ โปร่งใส แพลตฟอร์มที่ให้บริการ สล็อต PG ควรมี ความปลอดภัยสูง
สรุป
สล็อต PG เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน ระบบลื่นไหล และการทำธุรกรรมที่ ทันใจ ผู้เล่นสามารถเริ่มต้นได้ ทันที ฝากถอนสะดวก และเลือกเกมได้ ครบทุกหมวด เหมาะสำหรับ ทั้งมือใหม่และมือโปร ในโลกของเกมสล็อตออนไลน์
pg
TKBNEKO เปิดประสบการณ์ใหม่แห่งการเดิมพันออนไลน์ ฝาก-ถอนไว ด้วยระบบสแกน QR Code
ในยุคที่ โลกออนไลน์พัฒนาอย่างรวดเร็ว TKBNEKO ขอเป็นส่วนหนึ่งในการปฏิวัติวงการเกม ด้วยระบบการให้บริการที่ ล้ำสมัย เสถียร และ ตรวจสอบได้ พร้อมต้อนรับสมาชิกทุกท่านสู่ มิติใหม่แห่งความสนุก ที่ เปิดโอกาสให้ทุกคนสร้างรายได้
เพราะอะไรหลายคนจึงเลือก TKBNEKO
แพลตฟอร์มของเรารวบรวมเกมที่ได้มาตรฐาน โดยเฉพาะเกมที่ ผ่านการรับรองจากสถาบันที่น่าเชื่อถือ และ ได้มาตรฐานสากล เพื่อให้ผู้เล่นทุกคน สบายใจ ได้ว่า จะได้รับความเพลิดเพลินกับเกมที่ ยุติธรรม ข้อมูลไม่รั่วไหล และ ตอบโจทย์ผู้เล่นยุคใหม่
จุดเด่นของระบบฝาก-ถอน
ระบบฝากถอนถูกพัฒนาให้ใช้งานง่าย เพื่อให้คุณ โฟกัสกับความสนุกได้อย่างเต็มที่
ฝากขั้นต่ำ: เริ่มต้นเพียง 1 บาท
ถอนขั้นต่ำ: 1 บาท
เวลาฝากเงิน: เงินเข้าภายใน 3 วินาที
ยอดจำกัดการถอน: ไม่มีลิมิตการถอนรายวัน
ธุรกรรมสะดวก แค่สแกนคิวอาร์
เพียงคุณสแกน โค้ดคิวอาร์ ระบบของเราจะ ประมวลผลอย่างรวดเร็ว ขั้นต่ำเพียง 100 บาท และสามารถฝากได้สูงถึง ไม่เกิน 500,000 บาทต่อครั้ง มาร่วมสนุกกันได้แล้ววันนี้ กับ แพลตฟอร์มของเรา ที่ ใช้งานง่าย ทำกำไรได้รวดเร็ว
เกมยอดนิยมรวมไว้ในที่เดียว
แพลตฟอร์มของเราครอบคลุมทุกแนวเกม รองรับทุกความชอบของผู้เล่น
สล็อต: หลากหลายธีม แจ็คพอตรอคุณอยู่
เกมสด: ดีลเลอร์ถ่ายทอดสดตลอดเวลา
กีฬา: เดิมพันกับแมตช์การแข่งขันจากทั่วโลก
ยิงปลา: เกมยิงปลาสุดมันส์ ได้เงินจริง
ติดตามโปรโมชั่นและสิทธิพิเศษ
อย่าลืมแวะมาเยี่ยมชมที่หน้า โปรโมชันล่าสุด เพื่อรับ โบนัสสุดคุ้ม ที่เรามอบให้สมาชิกทุกท่าน นอกจากนี้ยังมีระบบ VIP สำหรับลูกค้าคนสำคัญ และช่องทาง พาร์ทเนอร์ สำหรับผู้ที่สนใจสร้างรายได้ร่วมกับเรา
ฝ่ายบริการลูกค้า
หากมี ข้อสงสัย หรือ ความคิดเห็น สามารถติดต่อทีมงานของเราได้ตลอด 24 ชั่วโมงที่หน้า ศูนย์ช่วยเหลือ และ ข้อเสนอแนะ ทีมงาน ของเรา ยินดีให้บริการทุกท่านด้วยใจ
ทดลองเล่นสล็อต pg เว็บ ตรง”
pg slot แพลตฟอร์มเกมสล็อตยอดนิยม ใช้งานง่าย ฝากถอนรวดเร็ว
คำค้นหา pg slot กำลังได้รับความนิยมอย่างต่อเนื่อง ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น แบรนด์เกมที่โดดเด่น ด้าน งานภาพคุณภาพสูง ความ ลื่นไหล และ โอกาสรับกำไรที่ดี เกมของ PG พัฒนาโดยผู้ให้บริการชั้นนำ ที่รองรับการเล่นทั้งบน โทรศัพท์มือถือ และ คอมพิวเตอร์
ความโดดเด่น ของ pg slot
สล็อต PG เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ โหลดเร็ว เล่นผ่าน ระบบอัตโนมัติ และรองรับ ทุกแพลตฟอร์ม เข้าเล่นผ่านเว็บได้เลย ผู้เล่นสามารถเข้าเล่นผ่าน หน้าเว็บ ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ 3D ให้ความคมชัด พร้อมเอฟเฟกต์ สมจริง
คุณสมบัติหลักของเกม PG Slot ได้แก่
ระบบโบนัสและฟรีสปินหลากหลายรูปแบบ
Multiplier
เล่นฟรีก่อนเติมเงิน
มีเมนูภาษาไทย
ฝากถอนง่าย ไม่ต้องรอนาน
แพลตฟอร์ม PG Slot มักมี การฝาก-ถอน ออโต้ตลอด 24 ชม. ขั้นต่ำเริ่มต้นเพียง 1 บาท ขึ้นอยู่กับ ระบบของผู้ให้บริการ การทำรายการใช้เวลา ไม่กี่วินาที ผ่าน QR Code หรือระบบ แอปธนาคาร ทำให้ธุรกรรมเป็นไปอย่าง ต่อเนื่อง
หมวดเกมฮิต ใน PG Slot
เกม PG Slot มีธีมหลากหลาย เช่น
ธีม เทพเจ้า
ธีม ลุยด่าน
ธีม เอเชียและโชคลาภ
ธีม Animal
หลายคนชอบเกมที่โบนัสเข้าไว พร้อมระบบ Special Feature และ ระบบจ่ายคุ้มค่า เหมาะกับทั้ง มือใหม่ และ สายสล็อตจริงจัง
ความปลอดภัย
pg slot พัฒนาในระบบสากล มีการ เข้ารหัสข้อมูล และใช้ระบบสุ่มผล Random Number Generator เพื่อให้ผลลัพธ์ โปร่งใส แพลตฟอร์มที่ให้บริการ pg slot ควรมี ทีมซัพพอร์ต 24 ชม.
บทสรุปท้ายบท
สล็อต PG เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน กราฟิกคุณภาพ และการทำธุรกรรมที่ ทันใจ ผู้เล่นสามารถเริ่มต้นได้ ไม่ซับซ้อน ฝากถอนสะดวก และเลือกเกมได้ ครบทุกหมวด เหมาะสำหรับ ทุกระดับประสบการณ์ ในโลกของเกมสล็อตออนไลน์
สล็อต PG สล็อตยอดฮิต เล่นง่าย ฝากถอนเร็ว
คำค้นหา สล็อต PG ถูกค้นหามากขึ้นเรื่อยๆ ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น ผู้ให้บริการเกมสล็อตที่มาแรง ด้าน ภาพและเอฟเฟกต์ ความ ลื่นไหล และ โอกาสรับกำไรที่ดี เกมของ PG ออกแบบโดยทีมงานมืออาชีพ ที่รองรับการเล่นทั้งบน โทรศัพท์มือถือ และ คอมพิวเตอร์
ความโดดเด่น ของ สล็อต PG
PG Slot เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ เข้าเกมไว เล่นผ่าน ระบบเว็บ และรองรับ ทุกอุปกรณ์ ไม่ต้องติดตั้งเพิ่มเติม ผู้เล่นสามารถเข้าเล่นผ่าน Browser ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ เอฟเฟกต์ 3 มิติ ให้ความคมชัด พร้อมเอฟเฟกต์ จัดเต็ม
คุณสมบัติหลักของเกม PG Slot ได้แก่
ระบบโบนัสและฟรีสปินหลากหลายรูปแบบ
Multiplier
โหมดทดลองเล่นฟรี
รองรับภาษาไทยเต็มรูปแบบ
ระบบฝากถอนสะดวก ไม่ต้องรอนาน
แพลตฟอร์ม สล็อต PG โดยทั่วไปให้บริการ การฝาก-ถอน อัตโนมัติ 24 ชั่วโมง ขั้นต่ำเริ่มต้นเพียง 1 บาท ขึ้นอยู่กับ ระบบของผู้ให้บริการ การทำรายการใช้เวลา ไม่กี่วินาที ผ่าน คิวอาร์โค้ด หรือระบบ แอปธนาคาร ทำให้ธุรกรรมเป็นไปอย่าง ไม่สะดุด
ประเภทเกมยอดนิยม ใน pg slot
เกม pg slot มีธีมหลากหลาย เช่น
ธีม แฟนตาซี
ธีม ลุยด่าน
ธีม โชคลาภ
ธีม ธรรมชาติ
หลายคนชอบเกมที่โบนัสเข้าไว พร้อมระบบ Special Feature และ ระบบจ่ายคุ้มค่า เหมาะกับทั้ง คนเพิ่งเล่น และ ผู้เล่นที่มีประสบการณ์
มาตรฐานระบบ
สล็อต PG มีมาตรฐานรองรับ มีการ ปกป้องข้อมูลผู้เล่น และใช้ระบบสุ่มผล RNG เพื่อให้ผลลัพธ์ โปร่งใส แพลตฟอร์มที่ให้บริการ สล็อต PG ควรมี ระบบดูแลข้อมูล
โดยภาพรวม
PG Slot เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน ระบบลื่นไหล และการทำธุรกรรมที่ ไว ผู้เล่นสามารถเริ่มต้นได้ ง่าย ฝากถอนสะดวก และเลือกเกมได้ จำนวนมาก เหมาะสำหรับ ทั้งมือใหม่และมือโปร ในโลกของเกมสล็อตออนไลน์
https://medium.com/@ratypw/ทดลองเล่นสล็อต-pg-70cdb1132344
ทดลองเล่นสล็อต pg เว็บ ตรง”
PG Slot เกมสล็อตออนไลน์ที่คนค้นหาเยอะ เล่นง่าย ฝากถอนเร็ว
คำค้นหา pg slot กำลังได้รับความนิยมอย่างต่อเนื่อง ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น ค่ายเกมที่มีชื่อเสียง ด้าน กราฟิก ความ นิ่งไม่สะดุด และ ระบบจ่ายที่ดึงดูด เกมของ PG ผลิตโดยค่ายมาตรฐาน ที่รองรับการเล่นทั้งบน โทรศัพท์มือถือ และ เดสก์ท็อป
จุดเด่น ของ pg slot
สล็อต PG เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ เข้าเกมไว เล่นผ่าน ระบบออนไลน์ และรองรับ ทุกอุปกรณ์ ไม่ต้องติดตั้งเพิ่มเติม ผู้เล่นสามารถเข้าเล่นผ่าน Browser ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ เอฟเฟกต์ 3 มิติ ให้ความคมชัด พร้อมเอฟเฟกต์ สมจริง
คุณสมบัติหลักของเกม pg slot ได้แก่
มีรอบโบนัสให้ลุ้นบ่อย
Multiplier
เล่นฟรีก่อนเติมเงิน
มีเมนูภาษาไทย
ระบบฝากถอนสะดวก ทันใจ
แพลตฟอร์ม pg slot ส่วนใหญ่รองรับ การฝาก-ถอน อัตโนมัติ 24 ชั่วโมง ขั้นต่ำเริ่มต้นเพียง 1 บาท ขึ้นอยู่กับ ระบบของผู้ให้บริการ การทำรายการใช้เวลา รวดเร็วมาก ผ่าน คิวอาร์โค้ด หรือระบบ แอปธนาคาร ทำให้ธุรกรรมเป็นไปอย่าง ไม่สะดุด
ประเภทเกมยอดนิยม ใน PG Slot
เกม pg slot มีธีมหลากหลาย เช่น
ธีม เทพเจ้า
ธีม Adventure
ธีม เอเชียและโชคลาภ
ธีม สัตว์และธรรมชาติ
เกมยอดนิยมมักเป็นเกมที่แตกง่าย พร้อมระบบ ฟีเจอร์พิเศษ และ ระบบจ่ายคุ้มค่า เหมาะกับทั้ง คนเพิ่งเล่น และ ผู้เล่นมือโปร
ความน่าเชื่อถือ
PG Slot ใช้ระบบที่ได้มาตรฐาน มีการ เข้ารหัสข้อมูล และใช้ระบบสุ่มผล RNG เพื่อให้ผลลัพธ์ ยุติธรรม แพลตฟอร์มที่ให้บริการ PG Slot ควรมี ระบบดูแลข้อมูล
โดยภาพรวม
pg slot เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน กราฟิกคุณภาพ และการทำธุรกรรมที่ ไว ผู้เล่นสามารถเริ่มต้นได้ ทันที ฝากถอนสะดวก และเลือกเกมได้ หลากหลายแนว เหมาะสำหรับ ผู้เล่นทุกสไตล์ ในโลกของเกมสล็อตออนไลน์
ทดลองเล่นสล็อต pg ฟรี pg slot สล็อตยอดฮิต ใช้งานง่าย ฝากถอนรวดเร็ว
คำค้นหา สล็อต PG กำลังได้รับความนิยมอย่างต่อเนื่อง ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น แบรนด์เกมที่โดดเด่น ด้าน งานภาพคุณภาพสูง ความ นิ่งไม่สะดุด และ ระบบจ่ายที่ดึงดูด เกมของ PG ออกแบบโดยทีมงานมืออาชีพ ที่รองรับการเล่นทั้งบน โทรศัพท์มือถือ และ คอมพิวเตอร์
ข้อดี ของ สล็อต PG
สล็อต PG เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ เปิดเกมได้ทันที เล่นผ่าน ระบบเว็บ และรองรับ ทั้ง iOS และ Android เข้าเล่นผ่านเว็บได้เลย ผู้เล่นสามารถเข้าเล่นผ่าน หน้าเว็บ ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ เอฟเฟกต์ 3 มิติ ให้ความคมชัด พร้อมเอฟเฟกต์ จัดเต็ม
คุณสมบัติหลักของเกม pg slot ได้แก่
มีรอบโบนัสให้ลุ้นบ่อย
ระบบตัวคูณ
โหมดทดลองเล่นฟรี
รองรับภาษาไทยเต็มรูปแบบ
ระบบการเงินรวดเร็ว ไม่ต้องรอนาน
แพลตฟอร์ม PG Slot โดยทั่วไปให้บริการ การฝาก-ถอน ออโต้ตลอด 24 ชม. ขั้นต่ำเริ่มต้นเพียง 10 บาท ขึ้นอยู่กับ กติกาแต่ละแพลตฟอร์ม การทำรายการใช้เวลา ไม่กี่วินาที ผ่าน สแกน QR หรือระบบ Mobile Banking ทำให้ธุรกรรมเป็นไปอย่าง ต่อเนื่อง
หมวดเกมฮิต ใน pg slot
เกม สล็อต PG มีธีมหลากหลาย เช่น
ธีม เทพเจ้า
ธีม ลุยด่าน
ธีม โชคลาภ
ธีม ธรรมชาติ
หลายคนชอบเกมที่โบนัสเข้าไว พร้อมระบบ โบนัสรอบพิเศษ และ ระบบจ่ายคุ้มค่า เหมาะกับทั้ง มือใหม่ และ สายสล็อตจริงจัง
ความน่าเชื่อถือ
pg slot มีมาตรฐานรองรับ มีการ เข้ารหัสข้อมูล และใช้ระบบสุ่มผล Random Number Generator เพื่อให้ผลลัพธ์ ตรวจสอบได้ แพลตฟอร์มที่ให้บริการ PG Slot ควรมี ความปลอดภัยสูง
สรุป
สล็อต PG เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน ระบบลื่นไหล และการทำธุรกรรมที่ รวดเร็ว ผู้เล่นสามารถเริ่มต้นได้ ง่าย ฝากถอนสะดวก และเลือกเกมได้ ครบทุกหมวด เหมาะสำหรับ ทุกระดับประสบการณ์ ในโลกของเกมสล็อตออนไลน์
ทดลองเล่นสล็อต pg ซื้อฟรีสปิน
ทดลองเล่นสล็อต pg ฟรี PG Slot สล็อตยอดฮิต ใช้งานง่าย ฝากถอนรวดเร็ว
คำค้นหา สล็อต PG กำลังได้รับความนิยมอย่างต่อเนื่อง ในกลุ่มผู้เล่นเกมสล็อตออนไลน์ เพราะเป็น แบรนด์เกมที่โดดเด่น ด้าน งานภาพคุณภาพสูง ความ ลื่นไหล และ ระบบจ่ายที่ดึงดูด เกมของ PG ออกแบบโดยทีมงานมืออาชีพ ที่รองรับการเล่นทั้งบน สมาร์ทโฟน และ พีซี
จุดเด่น ของ PG Slot
PG Slot เป็นเกมสล็อตออนไลน์ที่ออกแบบมาให้ เข้าเกมไว เล่นผ่าน ระบบออนไลน์ และรองรับ ทุกแพลตฟอร์ม ไม่ต้องดาวน์โหลดแอป ผู้เล่นสามารถเข้าเล่นผ่าน Browser ได้ทันที ภาพและเสียงถูกพัฒนาในรูปแบบ เอฟเฟกต์ 3 มิติ ให้ความคมชัด พร้อมเอฟเฟกต์ สวยงาม
คุณสมบัติหลักของเกม pg slot ได้แก่
โบนัสและฟรีสปินหลายแบบ
Multiplier
โหมดทดลองเล่นฟรี
รองรับภาษาไทยเต็มรูปแบบ
ระบบฝากถอนสะดวก ทันใจ
แพลตฟอร์ม สล็อต PG โดยทั่วไปให้บริการ การฝาก-ถอน ฝากถอนตลอดเวลา ขั้นต่ำเริ่มต้นเพียง หลักหน่วย ขึ้นอยู่กับ ระบบของผู้ให้บริการ การทำรายการใช้เวลา ไม่กี่วินาที ผ่าน สแกน QR หรือระบบ Mobile Banking ทำให้ธุรกรรมเป็นไปอย่าง ต่อเนื่อง
หมวดเกมฮิต ใน PG Slot
เกม pg slot มีธีมหลากหลาย เช่น
ธีม แฟนตาซี
ธีม Adventure
ธีม เอเชียและโชคลาภ
ธีม Animal
เกมยอดนิยมมักเป็นเกมที่แตกง่าย พร้อมระบบ ฟีเจอร์พิเศษ และ อัตราการจ่ายที่สูง เหมาะกับทั้ง มือใหม่ และ ผู้เล่นมือโปร
ความปลอดภัย
สล็อต PG ใช้ระบบที่ได้มาตรฐาน มีการ รักษาความปลอดภัย และใช้ระบบสุ่มผล Random Number Generator เพื่อให้ผลลัพธ์ ยุติธรรม แพลตฟอร์มที่ให้บริการ pg slot ควรมี ทีมซัพพอร์ต 24 ชม.
บทสรุปท้ายบท
สล็อต PG เป็นตัวเลือกยอดนิยมสำหรับผู้ที่ต้องการเล่นสล็อตออนไลน์ ด้วยจุดเด่นด้าน ระบบลื่นไหล และการทำธุรกรรมที่ ทันใจ ผู้เล่นสามารถเริ่มต้นได้ ง่าย ฝากถอนสะดวก และเลือกเกมได้ หลากหลายแนว เหมาะสำหรับ ผู้เล่นทุกสไตล์ ในโลกของเกมสล็อตออนไลน์
мелбет приветственный бонус
Скачать Melbet: Android, iPhone и компьютер
Приложение Melbet объединяет ставки и казино в едином приложении. Пользователю доступны live-ставки, слоты, прямые трансляции, аналитика и операции по счёту. Загрузка занимает 1–2 минуты.
Android (APK)
Скачайте APK с официального сайта, запустите установщик и подтвердите установку. Если требуется включите доступ к установке сторонних приложений, затем войдите в аккаунт.
iOS (iPhone)
Перейдите в App Store, найдите «Melbet», нажмите «Получить», после установки выполните вход.
ПК
Откройте официальный сайт, войдите в личный кабинет и создайте ярлык на рабочий стол. Браузерная версия функционирует как отдельное приложение.
Функционал
Live-ставки с мгновенным обновлением линии, казино и слоты, прямые трансляции, аналитические данные, push-оповещения, регистрация за минуту и поддержка 24/7.
Бонусы
После загрузки доступны бонус на первый депозит, акционные коды и бесплатные ставки. Условия зависят от региона.
Безопасность
Скачивайте только с официального сайта, контролируйте адрес сайта, не сообщайте данные доступа третьим лицам и включите 2FA.
Загрузка выполняется быстро, после чего открывается полный доступ Melbet.
мелбет зеркало скачать на айфон
Скачать Melbet: Android, iOS и ПК
Мобильная версия Melbet включает ставки и казино в едином приложении. Доступны live-ставки, казино-игры, прямые трансляции, статистика и быстрые финансовые операции. Загрузка занимает 1–2 минуты.
Android (APK)
Скачайте APK с официального источника, откройте файл и подтвердите установку. Если требуется включите разрешение на установку из неизвестных источников, затем войдите в аккаунт.
iOS (iPhone)
Перейдите в App Store, введите в поиске «Melbet», нажмите «Получить», после установки выполните вход.
ПК
Перейдите официальный сайт, войдите в личный кабинет и создайте ярлык на рабочий стол. Веб-версия работает как полноценное приложение.
Функционал
Live-ставки с обновлением коэффициентов, игровой раздел с тысячами игр, прямые трансляции, подробная статистика, уведомления о матчах, регистрация за минуту и круглосуточная служба поддержки.
Бонусы
После загрузки доступны приветственный бонус, промокоды и бесплатные ставки. Правила начисления определяются регионом.
Безопасность
Скачивайте только с официальных источников, проверяйте домен, не передавайте пароль третьим лицам и активируйте двухфакторную аутентификацию.
Загрузка выполняется быстро, после чего открывается полный доступ Melbet.
ทดลองเล่นสล็อต pg ไม่ เด้ง
rufus Rufus is known as a lightweight, free, open-source utility designed to create bootable USB drives. It allows you to prepare a USB flash drive that can install an operating system, run diagnostic tools, or start a recovery environment. The program works without installation and can be opened right after download.
The primary purpose of Rufus is helping users to create bootable USB media from ISO images quickly and reliably. This allows users to install or run operating systems directly from a USB flash drive without the need for DVDs. The tool supports a large number of operating systems and service utilities, which makes it practical for both regular users and system administrators.
Rufus runs on computers with Microsoft Windows, starting from Windows 7. Both 32-bit and 64-bit versions are supported, and there is also a version available for ARM64 architecture.
The software lets users create bootable USB drives from many different ISO images. It can be used to prepare a USB drive for installing Windows 11, Windows 10, Windows 8.1, or Windows 7, as well as various Linux distributions. Rufus also works with DOS systems and other recovery or maintenance tools commonly used for troubleshooting computers.
One of the included features of Rufus is the ability to download official Windows ISO images directly from Microsoft servers. This allows users to obtain original installation images for Windows 8.1, Windows 10, and Windows 11 without searching for them on third-party websites.
In addition to creating bootable drives, Rufus can format USB devices. It supports several file systems including FAT32, NTFS, exFAT, UDF, and ReFS. This flexibility allows the USB drive to be prepared for different use cases and compatibility requirements.
Rufus supports both legacy BIOS systems and modern UEFI environments. Because of this, bootable drives created with Rufus can work on older computers as well as newer systems that use UEFI and Secure Boot.
Another feature included in Rufus is Windows To Go support. This option allows users to run a full Windows environment directly from a USB drive. It can be useful for testing systems, performing maintenance, or working on multiple computers without installing Windows on the internal drive.
Rufus also provides the option to bypass certain Windows 11 installation requirements. When creating an installation USB, the program can disable checks for TPM 2.0, Secure Boot, and minimum RAM requirements. This makes it possible to install Windows 11 on computers that would otherwise not meet the official hardware requirements.
One of the reasons Rufus has become popular is its speed and simplicity. The program is extremely small, about 1.9 MB in size, and runs as a portable application without installation. It is distributed under the GPL v3 open-source license, supports more than 70 languages, and contains no advertisements, bundled software, or tracking components.
Rufus works with a large number of ISO images. These include multiple versions of Windows, Windows Server editions, FreeDOS, and various system tools such as GParted, Hiren’s Boot CD, Parted Magic, and Clonezilla. Because of this wide compatibility, the program can be used not only for installing operating systems but also for disk management, data recovery, and system maintenance tasks.
To use Rufus, a computer running Windows 7 or later and a USB flash drive are required. The program does not need to be installed. Users simply download the executable file, run it, select the ISO image they want to use, and create a bootable USB drive. Due to its simplicity, speed, and reliability, Rufus remains one of the most widely used tools for creating bootable USB drives.
скачать мелбет с казино
Установить приложение Melbet: APK, iOS и компьютер
Приложение Melbet включает ставки и казино в одном интерфейсе. Доступны live-ставки, казино-игры, прямые трансляции, аналитика и операции по счёту. Загрузка занимает несколько минут.
Android (APK)
Загрузите APK с официального сайта, запустите установщик и подтвердите установку. Если требуется включите разрешение на установку из неизвестных источников, затем авторизуйтесь.
iOS (iPhone)
Откройте App Store, введите в поиске «Melbet», нажмите «Получить», после установки авторизуйтесь в системе.
ПК
Перейдите официальный сайт, войдите в личный кабинет и добавьте ярлык на рабочий стол. Веб-версия работает как отдельное приложение.
Функционал
Live-ставки с мгновенным обновлением линии, казино и слоты, просмотр матчей, аналитические данные, уведомления о матчах, быстрая регистрация и круглосуточная служба поддержки.
Бонусы
После установки доступны бонус на первый депозит, промокоды и фрибеты. Условия зависят от региона.
Безопасность
Скачивайте только с официальных источников, проверяйте домен, не сообщайте данные доступа третьим лицам и активируйте двухфакторную аутентификацию.
Загрузка выполняется быстро, после чего доступен весь функционал Melbet.
ричтрак для высотного склада купить
скачать melbet казино
Скачать Melbet: Android, iOS и компьютер
Приложение Melbet объединяет букмекерскую контору и казино в одном интерфейсе. Доступны live-ставки, казино-игры, онлайн-трансляции, аналитика и операции по счёту. Установка занимает 1–2 минуты.
Android (APK)
Загрузите APK с официального источника, запустите установщик и завершите установку. При необходимости включите доступ к установке сторонних приложений, затем авторизуйтесь.
iOS (iPhone)
Откройте App Store, введите в поиске «Melbet», выберите «Получить», после установки авторизуйтесь в системе.
ПК
Откройте официальный сайт, войдите в личный кабинет и создайте ярлык на рабочий стол. Веб-версия работает как отдельное приложение.
Функционал
Live-ставки с обновлением коэффициентов, казино и слоты, просмотр матчей, подробная статистика, push-оповещения, регистрация за минуту и круглосуточная служба поддержки.
Бонусы
После установки доступны бонус на первый депозит, промокоды и бесплатные ставки. Условия зависят от региона.
Безопасность
Загружайте только с официального сайта, проверяйте домен, не сообщайте данные доступа третьим лицам и включите 2FA.
Установка занимает несколько минут, после чего открывается полный доступ Melbet.
http://silichem.co.kr/bbs/board.php?bo_table=free&wr_id=851271
казино х зеркало на сегодня
вулкан вегас официальный
леонбетс скачать
раменбет играть онлайн бесплатно
казино джой
блэкджек игра на реальные деньги
рейтинг лучших казино
колесо фортуны на деньги
Tür öffnen Worms
폰테크
폰테크라는 방식은 급하게 현금이 필요할 때 빠르게 검토되는 방식으로 소개됩니다. 요즘은 비대면 진행과 당일 입금, 미납요금 대납, 전국 상담 같은 항목이 같이 강조되면서 소개 방식도 많아졌습니다. 다만 검토할 때는 속도보다 절차를 먼저 확인해야 합니다. 어떤 절차로 접수되고 진행되고 입금되는지 보는 것이 우선입니다.
비대면 방식의 폰테크는 직접 방문하지 않고 상담과 접수, 진행 안내를 원격으로 처리하는 형태가 많습니다. 수도권뿐 아니라 강원도, 충청도, 전라도, 경상도, 제주까지 전국 단위 상담을 내세우는 경우도 많습니다. 방문 부담이 적다는 점은 분명 편리하지만, 절차가 단순해 보일수록 조건 확인은 더 정확해야 합니다.
이런 서비스 안내에서는 보통 당일 진행, 당일 입금, 24시간 상담, 365일 연중무휴 같은 표현이 반복됩니다. 하지만 핵심은 문구가 아니라 진행 내용의 구체성입니다. 어떤 기종을 다루는지, 조건이 어떻게 정해지는지, 어떤 방식으로 진행 가능한지, 입금 시점이 언제인지까지 확인돼야 합니다.
진행 흐름은 대체로 비슷합니다. 전화·문자·카카오톡으로 접수를 받고, 조건과 기종을 확인한 다음, 원하는 거래 방식을 선택하고, 기기 수령 이후 당일 지급으로 연결되는 형태입니다. 단계 수는 적어 보여도 실제로는 각 단계마다 확인할 내용이 다릅니다. 특히 상담 단계에서 본인 상황에 맞는 진행 형태와 가능 조건을 분명히 해야 뒤에서 꼬이지 않습니다.
전국 대응을 강조하는 업체들은 지역명을 세세하게 나열하는 경우가 많습니다. 이런 나열 방식은 지역 기반 검색에 맞춰진 구성이며, 방문자에게 본인 지역도 포함된다는 느낌을 줍니다. 지역명과 서비스명을 붙인 표현이 반복되는 이유도 여기에 있습니다.
상담 채널은 보통 대표전화, 카카오톡, 상담신청 버튼처럼 바로 연결되는 구조로 잡힙니다. 여기에 정식등록업체, 비대면 당일입금, 1:1 상담 같은 문구가 붙습니다. 다만 판단 기준은 광고 문구가 아니라 운영 정보와 절차 설명입니다.
결국 폰테크 소개에서 핵심은 세 가지입니다. 빠른 진행 가능성, 비대면과 전국 대응, 단순한 진행 흐름이 주된 포인트입니다. 반대로 실제 확인 포인트는 속도가 아니라 조건과 절차, 지역 대응 범위입니다.
폰테크
폰테크라는 방식은 급하게 현금이 필요할 때 빠르게 검토되는 방식으로 거론됩니다. 요즘은 비대면 진행, 당일 입금, 미납요금 대납, 전국 상담 같은 요소가 같이 노출되면서 관련 안내도 더 많아졌습니다. 그렇다고 해서 검토할 때는 빠르다는 말보다 진행 구조를 먼저 봐야 합니다. 어떤 절차로 접수되고 진행되고 입금되는지 보는 것이 우선입니다.
비대면 폰테크는 방문 없이 상담, 접수, 진행 안내까지 상당 부분을 원격으로 처리하는 형태가 중심입니다. 서울, 경기, 인천 같은 수도권뿐 아니라 강원, 충청, 전라, 경상, 제주까지 전국 대응을 강조하는 곳도 많습니다. 방문 부담이 적다는 점은 분명 편리하지만, 절차가 단순해 보일수록 조건 확인은 더 정확해야 합니다.
이런 서비스 안내에서는 당일 진행, 당일 입금, 24시간 상담, 연중무휴 같은 문구가 자주 보입니다. 중요한 것은 표현보다 실제 진행 방식입니다. 어떤 기종을 기준으로 상담하는지, 매입 조건이 어떻게 잡히는지, 비대면·방문·출장·대납 중 어떤 방식이 가능한지, 접수 후 입금은 언제 이뤄지는지까지 정리돼 있어야 합니다.
진행 흐름은 대체로 비슷합니다. 전화, 문자, 카카오톡으로 상담 신청을 받고, 그다음 기종과 조건을 맞춰 상담을 진행하고, 방문·출장·비대면·대납 중 방식을 선택하고, 기기 수령 후 당일 지급으로 이어지는 구조입니다. 순서는 짧아 보여도 실제 확인 항목은 적지 않습니다. 특히 상담 단계에서 본인 상황에 맞는 진행 형태와 가능 조건을 분명히 해야 뒤에서 꼬이지 않습니다.
전국 대응을 강조하는 업체들은 서울, 부산, 대구, 경기, 인천, 광주, 울산, 대전, 세종, 강원, 충북, 충남, 전북, 전남, 경북, 경남, 제주처럼 지역명을 촘촘히 배치합니다. 이런 방식은 지역 키워드 노출에 유리하고, 사용자에게 해당 지역에서도 진행 가능하다는 인상을 줍니다. 이 때문에 지역명 조합 키워드가 반복적으로 쓰입니다.
문의 경로는 대표전화, 카카오톡, 상담신청 버튼처럼 즉시 연결되는 방식이 많습니다. 보통 이런 채널 옆에는 신속 진행이나 1:1 상담 문구가 함께 배치됩니다. 하지만 실제 판단 기준은 문구가 아니라 운영 정보, 절차 설명, 상담 내용의 명확성입니다.
요약하면 핵심 포인트는 세 가지입니다. 빠른 진행 가능성, 비대면과 전국 대응, 단순한 진행 흐름이 주된 포인트입니다. 이용자 기준에서는 빠르다는 말보다 조건과 절차를 먼저 보는 편이 맞습니다.
폰테크
폰테크는 자금이 급히 필요한 상황에서 자주 검토되는 수단으로 소개됩니다. 요즘은 비대면 진행, 당일 입금, 미납요금 대납, 전국 상담 같은 요소가 같이 노출되면서 소개 방식도 많아졌습니다. 다만 실제로 알아볼 때는 속도보다 절차를 먼저 확인해야 합니다. 어떻게 접수되고, 어떤 방식으로 진행되며, 입금까지 어떤 절차를 거치는지 확인하는 쪽이 더 중요합니다.
비대면 폰테크는 방문 없이 상담부터 접수, 진행 안내까지 이어지는 구조가 많습니다. 수도권뿐 아니라 강원, 충청, 전라, 경상, 제주까지 전국 상담이 가능하다고 안내하는 경우가 많습니다. 직접 움직이지 않아도 된다는 점은 편하지만, 보기보다 단순해 보여도 조건 확인은 더 꼼꼼해야 합니다.
폰테크·가개통 안내 문구에서는 당일 진행, 당일 입금, 24시간 상담, 연중무휴 같은 문구가 자주 보입니다. 하지만 핵심은 문구가 아니라 진행 내용의 구체성입니다. 상담 기준 기종, 매입 조건, 가능한 진행 방식, 접수 후 입금 시점까지 분명해야 합니다.
전체 진행 순서는 대체로 비슷합니다. 전화나 문자, 카카오톡으로 상담을 시작한 뒤, 그다음 기종과 조건을 맞춰 상담을 진행하고, 원하는 거래 방식을 선택하고, 기기 수령 이후 당일 지급으로 연결되는 형태입니다. 순서는 짧아 보여도 실제 확인 항목은 적지 않습니다. 특히 상담 단계에서 본인 상황에 맞는 진행 형태와 가능 조건을 분명히 해야 뒤에서 꼬이지 않습니다.
전국 서비스를 내세우는 곳들은 서울, 부산, 대구, 경기, 인천, 광주, 울산, 대전, 세종, 강원, 충북, 충남, 전북, 전남, 경북, 경남, 제주처럼 지역명을 촘촘히 배치합니다. 이런 구성은 지역 검색에 강하고, 사용자에게 해당 지역에서도 진행 가능하다는 인상을 줍니다. 지역명과 서비스명을 붙인 표현이 반복되는 이유도 여기에 있습니다.
문의 경로는 대표전화, 카카오톡, 상담신청 버튼처럼 즉시 연결되는 방식이 많습니다. 보통 이런 채널 옆에는 신속 진행이나 1:1 상담 문구가 함께 배치됩니다. 하지만 실제 판단 기준은 문구가 아니라 운영 정보, 절차 설명, 상담 내용의 명확성입니다.
결국 폰테크 소개에서 핵심은 세 가지입니다. 빠른 진행 가능성, 비대면과 전국 대응, 단순한 진행 흐름이 주된 포인트입니다. 반대로 실제 확인 포인트는 속도가 아니라 조건과 절차, 지역 대응 범위입니다.
폰테크
폰테크는 자금이 급히 필요한 상황에서 자주 검토되는 수단으로 거론됩니다. 최근 들어 비대면 진행과 당일 입금, 미납요금 대납, 전국 상담 같은 항목이 같이 강조되면서 소개 방식도 많아졌습니다. 하지만 검토할 때는 속도보다 구조를 먼저 봐야 합니다. 어떻게 접수되고, 어떤 방식으로 진행되며, 입금까지 어떤 절차를 거치는지 확인하는 쪽이 더 중요합니다.
비대면 방식의 폰테크는 직접 방문하지 않고 상담과 접수, 진행 안내를 원격으로 처리하는 형태가 많습니다. 수도권뿐 아니라 강원, 충청, 전라, 경상, 제주까지 전국 단위 상담을 내세우는 경우도 많습니다. 방문 부담이 적다는 점은 분명 편리하지만, 간단해 보일수록 조건은 더 세밀하게 봐야 합니다.
이런 서비스 안내에서는 속도와 상시 상담을 강조하는 표현이 반복되는 경우가 많습니다. 하지만 핵심은 문구가 아니라 진행 내용의 구체성입니다. 어떤 기종을 기준으로 상담하는지, 매입 조건이 어떻게 잡히는지, 비대면·방문·출장·대납 중 어떤 방식이 가능한지, 접수 후 입금은 언제 이뤄지는지까지 정리돼 있어야 합니다.
전체 진행 순서는 대체로 비슷합니다. 전화·문자·카카오톡으로 접수를 받고, 조건과 기종을 확인한 다음, 방문, 출장, 비대면, 대납 중 방식을 고른 뒤, 기기 수령 후 당일 지급으로 이어지는 구조입니다. 단계 수는 적어 보여도 실제로는 각 단계마다 확인할 내용이 다릅니다. 특히 처음 상담 단계에서 가능 조건을 분명히 해두는 것이 중요합니다.
전국 대응을 강조하는 업체들은 서울, 부산, 대구, 경기, 인천, 광주, 울산, 대전, 세종, 강원, 충북, 충남, 전북, 전남, 경북, 경남, 제주처럼 지역명을 촘촘히 배치합니다. 이런 나열 방식은 지역 기반 검색에 맞춰진 구성이며, 이용자에게 자기 지역도 가능하다는 인식을 줍니다. 서울 폰테크, 경기 폰테크, 인천 가개통 같은 표현이 반복되는 이유도 여기에 있습니다.
문의 경로는 대표전화, 카카오톡, 상담신청 버튼처럼 즉시 연결되는 방식이 많습니다. 그리고 여기에 정식등록업체, 당일입금, 1:1 상담 같은 표현이 더해집니다. 다만 판단 기준은 광고 문구가 아니라 운영 정보와 절차 설명입니다.
정리하면 핵심은 세 가지입니다. 급전 상황에서 빠르게 진행할 수 있다는 점, 비대면과 전국 상담이 가능하다는 점, 상담 신청부터 지급까지 흐름이 단순하다는 점입니다. 반대로 이용자 입장에서는 속도보다 조건, 절차, 지역 대응 범위, 상담 내용의 명확성을 먼저 봐야 합니다.
Продуманный внешний вид играет ключевую роль в формировании образа.
Она помогает подчеркнуть индивидуальность и выглядеть гармонично.
Современный внешний вид влияет на то, как человека видят в обществе.
В повседневной жизни одежда может повышать самооценку.
https://ulmoda.ru/moda/2026-03-31-aksessuary-salvatore-ferragamo-ot-sumok-do-parfyumerii/
Хорошо подобранная одежда облегчает деловые встречи.
При этом важно учитывать собственный вкус и контекст.
Современные тенденции дают возможность экспериментировать.
В итоге, умение стильно одеваться влияет на общее восприятие личности.
폰테크
폰테크는 급하게 현금이 필요할 때 많이 찾는 방식으로 소개됩니다. 최근 들어 비대면 방식, 당일 입금, 미납요금 대납, 전국 상담 등이 같이 노출되면서 안내 문구도 늘어났습니다. 하지만 진행을 알아볼 때는 속도보다 절차를 먼저 확인해야 합니다. 어떤 절차로 접수되고 진행되고 입금되는지 보는 것이 우선입니다.
비대면 방식의 폰테크는 직접 방문하지 않고 상담과 접수, 진행 안내를 원격으로 처리하는 형태가 많습니다. 수도권뿐 아니라 강원, 충청, 전라, 경상, 제주까지 전국 상담이 가능하다고 안내하는 경우가 많습니다. 방문 부담이 적다는 점은 분명 편리하지만, 절차가 단순해 보일수록 조건 확인은 더 정확해야 합니다.
폰테크나 가개통 안내에서는 속도와 상시 상담을 강조하는 표현이 반복되는 경우가 많습니다. 중요한 것은 표현보다 실제 진행 방식입니다. 어떤 기종을 다루는지, 조건이 어떻게 정해지는지, 어떤 방식으로 진행 가능한지, 입금 시점이 언제인지까지 확인돼야 합니다.
보통 진행 구조는 크게 다르지 않습니다. 전화나 문자, 카카오톡으로 상담을 시작한 뒤, 조건과 기종을 확인한 다음, 원하는 거래 방식을 선택하고, 기기 수령 후 당일 지급으로 이어지는 구조입니다. 단계 수는 적어 보여도 실제로는 각 단계마다 확인할 내용이 다릅니다. 특히 상담 단계에서 본인 상황에 맞는 진행 형태와 가능 조건을 분명히 해야 뒤에서 꼬이지 않습니다.
전국 단위로 운영된다고 하는 곳들은 서울, 부산, 대구, 경기, 인천, 광주, 울산, 대전, 세종, 강원, 충북, 충남, 전북, 전남, 경북, 경남, 제주처럼 지역명을 촘촘히 배치합니다. 이런 방식은 지역 키워드 노출에 유리하고, 이용자에게 자기 지역도 가능하다는 인식을 줍니다. 이 때문에 지역명 조합 키워드가 반복적으로 쓰입니다.
상담 채널은 대체로 전화, 카카오톡, 신청 버튼 중심으로 구성됩니다. 보통 이런 채널 옆에는 신속 진행이나 1:1 상담 문구가 함께 배치됩니다. 다만 판단 기준은 광고 문구가 아니라 운영 정보와 절차 설명입니다.
결국 폰테크 소개에서 핵심은 세 가지입니다. 급전 상황에서 빠르게 진행할 수 있다는 점, 비대면과 전국 상담이 가능하다는 점, 상담 신청부터 지급까지 흐름이 단순하다는 점입니다. 반대로 실제 확인 포인트는 속도가 아니라 조건과 절차, 지역 대응 범위입니다.
cheap tobacco australia
Online Tobacco Sales in Australia: Between Health Warnings and “Cheap” Cigarettes
There is an online platform offering customers in Australia the option to purchase cigarettes and tobacco with delivery to their door. The website, which operates under the name Australia Tobacconist Hub, shows a clear inconsistency: heavy promotion of budget tobacco products alongside formal warnings about the health risks of tobacco use.
Available Items
The platform’s key customer base is people who smoke trying to cut costs. Key items on the price list include:
Double Happiness (?? ??) — $190 per carton (10 packets x 20’s)
Manchester Sapphire Blue – Dubai Version — $220 per block
Manchester Special Edition Flow Red – Dubai Edition — $250 per block
Manchester Blue Crush (Dubai Version) — $250 per carton
Dunhill Blue (UK Version) — $220 per carton
Dunhill Red – UK Edition — $190 per block
Benson and Hedges Gold — $160 per block
Zhongnanhai brand — $180 per carton
The seller stresses “competitive prices” (Cheap Tobacco Australia) and the offering of popular brands such as Marlboro, Manchester, Bossku, Double Happiness, and others.
Logistics and Payment
The seller claims to offer quick, dependable, and private shipping across Australia (Fast Tobacco Delivery Australia). They claim to accept bank transfers, USDT (cryptocurrency), PayPal, Wise, and other methods. Customer communication is conducted via WhatsApp, email, and other messaging apps — a typical practice in the unlicensed sector for internet cigarette shops.
A Strange Contrast
Interestingly, the same website that sells cigarettes (while formally warning that selling to persons under 18 is illegal) also shows a “STOP SMOKING” banner with an drawing of a cigarette passing through human lungs.
In a section titled “STOP TOBACCO”, the text reads:
“Giving up smoking is hard, but each attempt matters. Within minutes, your body begins to heal — and as time goes by, your health and vitality return. Let’s start today!”
This anti-smoking advice is placed near a list of items for sale selling cartons for $160–$250 and a call to action: “Purchase cigarettes online in Australia for the lowest price.” Such double messaging is characteristic of illegal or semi-legal cigarette sellers that try to feign social responsibility while continuing to sell addictive products.
Legal Risks
The text does not specify whether the seller holds a proper local permit for tobacco. Australia is known for having some of the strictest tobacco laws in the world, including standardised packaging rules and very large tobacco duties. The offer of “cheap” cigarettes — especially “Dubai Edition” or “UK Version” — often suggests untaxed, smuggled, or counterfeit goods.
Summary
The website in question is a clear illustration of a shadow online tobacco business. It exploits smokers’ desire to save money in the context of Australia’s high legal tobacco taxes, while masking itself with superficial “Stop Smoking” slogans and promises of good service. Potential buyers should keep in mind that buying unlicensed tobacco carries not only the chance of legal trouble but also a complete lack of quality or safety guarantees.
pg slot
แพลตฟอร์มสล็อตสมัยใหม่กำลังเปลี่ยนจากเกมหมุนวงล้อทั่วไปไปสู่ระบบออนไลน์ที่ใช้เทคโนโลยีขั้นสูง และใช้โครงสร้าง API แบบเรียลไทม์ร่วมกับระบบประมวลผลที่เสถียร ผู้เล่นจำนวนมากเริ่มเลือกใช้แพลตฟอร์มสล็อตเว็บตรง เพราะระบบตอบสนองได้รวดเร็วกว่าระบบตัวกลาง และช่วยลดปัญหาการดีเลย์ อาการเกมสะดุด รวมถึงข้อผิดพลาดของธุรกรรม
โครงสร้างสล็อต API ตรงจะส่งข้อมูลไปยังค่ายเกมหลักผ่านAPI โดยตรง ทำให้สถานะเกมและยอดเงินถูกส่งแบบอัตโนมัติโดยไม่ต้องผ่านหลายเซิร์ฟเวอร์ ส่งผลให้เกมโหลดเร็วขึ้น ลดความผิดพลาดระหว่างการหมุน และช่วยให้การคำนวณรางวัลทำงานได้ต่อเนื่องกว่าเดิม
อีกหนึ่งองค์ประกอบที่ทำให้ระบบนี้น่าสนใจคือระบบวอลเล็ตที่ซิงค์แบบเรียลไทม์ ผู้เล่นสามารถเติมเครดิตและถอนเงินได้ตลอดโดยไม่จำกัดช่วงเวลา โดยไม่จำเป็นต้องรอแอดมินตรวจสอบเหมือนเว็บตัวกลางแบบเดิม ทำให้การหมุนเวียนเครดิตมีความต่อเนื่องกว่าเดิม
เหตุผลหลักที่ผู้เล่นเลือกสล็อตเว็บตรงคือความน่าเชื่อถือและการตอบสนองที่รวดเร็ว เซิร์ฟเวอร์ที่ผูกกับระบบเกมต้นทางช่วยลดปัญหาการแทรกแซงผลลัพธ์ ผู้เล่นจึงเชื่อถือได้ว่าผลลัพธ์ของเกมมาจากระบบ RNG จริง
เมื่อดูในแง่ประสบการณ์ผู้ใช้ เว็บสมัยใหม่ยังมีการพัฒนาระบบแสดงผลบนสมาร์ตโฟนโดยเฉพาะ เช่น การเล่นแนวตั้ง การเปิดหน้าเกมโดยไม่หน่วง และระบบ Auto Resumeที่ช่วยกลับเข้าสู่เกมเดิมเมื่ออินเทอร์เน็ตหลุด
แพลตฟอร์มสล็อตยุคใหม่เริ่มใช้ระบบวิเคราะห์ข้อมูลอัตโนมัติ ร่วมกับระบบ Cloud Infrastructureและการเชื่อมต่อข้อมูลอัตโนมัติเพื่อรองรับปริมาณธุรกรรมจำนวนมาก บางระบบยังรองรับเทคโนโลยีบล็อกเชนเพื่อเพิ่มทางเลือกในการทำธุรกรรมและลดข้อจำกัดของระบบธนาคารแบบเดิม
แพลตฟอร์มเกมออนไลน์ประเภทสล็อตจึงกำลังเปลี่ยนจากแพลตฟอร์มที่เน้นแค่เกมและโปรโมชั่นไปสู่แพลตฟอร์มดิจิทัลที่ขับเคลื่อนด้วยข้อมูล โดยความเร็วและความแม่นยำของธุรกรรมกลายเป็นปัจจัยสำคัญในการเลือกแพลตฟอร์ม
เมื่อเทคโนโลยีพัฒนาเร็วขึ้นแพลตฟอร์มสล็อตจะยิ่งแข่งขันกันด้านคุณภาพ APIมากขึ้น ไม่ว่าจะเป็นการตอบสนองของหน้าเกม ระบบ AI วิเคราะห์พฤติกรรมผู้เล่น หรือระบบความปลอดภัยของข้อมูล ผู้ให้บริการที่มีAPI เชื่อมต่อโดยตรงและเชื่อมต่อกับค่ายเกมโดยตรงจะมีความน่าเชื่อถือมากกว่าเว็บทั่วไปที่ยังใช้ระบบตรวจสอบที่ไม่อัตโนมัติเต็มรูปแบบ
ผู้เล่นยุคใหม่จึงไม่ได้มองแค่โปรโมชั่นอีกต่อไป แต่เริ่มให้ความสำคัญกับความเสถียรของระบบ ความต่อเนื่องของระบบการเงิน และความพร้อมของระบบเมื่อต้องรองรับผู้เล่นจำนวนมาก
France Sahel
สล็อตเว็บตรง
สล็อตออนไลน์ยุคใหม่กำลังขยับออกจากระบบเกมหมุนวงล้อคลาสสิกไปสู่ระบบคาสิโนออนไลน์ที่เน้นความเสถียรและความเร็ว ซึ่งให้ความสำคัญกับโครงสร้าง API แบบเรียลไทม์ร่วมกับเซิร์ฟเวอร์ความเร็วสูง ผู้เล่นจำนวนมากเริ่มให้ความสนใจกับแพลตฟอร์มสล็อตเว็บตรง เพราะระบบตอบสนองได้รวดเร็วกว่าระบบตัวกลาง และช่วยลดปัญหาการประมวลผลช้า ความผิดพลาดระหว่างการหมุน รวมถึงข้อผิดพลาดของธุรกรรม
โครงสร้างสล็อต API ตรงจะรับส่งข้อมูลกับผู้ให้บริการเกมผ่านโหนด API ที่ไม่ผ่านตัวกลาง ทำให้ข้อมูลการเล่นถูกส่งแบบต่อเนื่องโดยไม่ต้องผ่านโครงสร้างที่เพิ่มความหน่วง ส่งผลให้เกมโหลดเร็วขึ้น ลดอาการค้างระหว่างเข้าโหมดพิเศษ และช่วยให้การคำนวณรางวัลทำงานได้ต่อเนื่องกว่าเดิม
อีกจุดสำคัญคือระบบฝากถอนอัตโนมัติ ผู้เล่นสามารถเติมเครดิตและถอนเงินได้ตลอดทั้งวัน โดยไม่จำเป็นต้องเสียเวลารอเจ้าหน้าที่เหมือนเว็บตัวกลางแบบเดิม ทำให้การฝากถอนระหว่างเล่นมีความแม่นยำกว่าเดิม
สาเหตุที่สล็อตเว็บตรงได้รับความนิยมคือความมั่นใจในผลลัพธ์และความเร็วของระบบ เซิร์ฟเวอร์ที่ผูกกับระบบเกมต้นทางช่วยลดความเสี่ยงจากการปรับแต่งข้อมูลระหว่างทาง ผู้เล่นจึงตรวจสอบได้ว่าผลลัพธ์ของเกมมาจากระบบ RNG จริง
เมื่อดูในแง่ประสบการณ์ผู้ใช้ เว็บสมัยใหม่ยังมีการพัฒนาUX/UI สำหรับมือถือโดยเฉพาะ เช่น หน้าจอที่ออกแบบให้ใช้มือเดียวได้สะดวก การโหลดหน้าแบบ Dynamic และระบบ Auto Resumeที่ช่วยคืนสถานะเกมเมื่อสัญญาณขาดช่วง
แพลตฟอร์มสล็อตยุคใหม่เริ่มใช้เครื่องมือวิเคราะห์แบบเรียลไทม์ ร่วมกับระบบ Cloud InfrastructureและAPI Syncเพื่อรองรับการเล่นต่อเนื่องของผู้เล่นหลายกลุ่ม บางระบบยังรองรับCrypto Paymentเพื่อเพิ่มความปลอดภัยของข้อมูลและลดปัญหาธุรกรรมล่าช้า
อุตสาหกรรมสล็อตออนไลน์จึงกำลังเปลี่ยนจากแพลตฟอร์มที่เน้นแค่เกมและโปรโมชั่นไปสู่ระบบเทคโนโลยีเต็มรูปแบบ โดยโครงสร้าง APIและความแม่นยำของธุรกรรมกลายเป็นปัจจัยสำคัญในการเลือกแพลตฟอร์ม
ต่อจากนี้แพลตฟอร์มสล็อตจะยิ่งแข่งขันกันด้านเสถียรภาพของแพลตฟอร์มมากขึ้น ไม่ว่าจะเป็นความเร็วในการโหลดเกม ระบบแนะนำเกมตามข้อมูลจริง หรือการเข้ารหัสธุรกรรม ผู้ให้บริการที่มีAPI เชื่อมต่อโดยตรงและเชื่อมต่อกับค่ายเกมโดยตรงจะได้เปรียบมากกว่าเว็บทั่วไปที่ยังใช้การเชื่อมต่อแบบเก่า
คนที่เลือกแพลตฟอร์มอย่างจริงจังจึงไม่ได้มองแค่โบนัสอีกต่อไป แต่เริ่มให้ความสำคัญกับมาตรฐานทางเทคนิคของแพลตฟอร์ม ความเร็วในการทำธุรกรรม และเสถียรภาพของแพลตฟอร์มระหว่างการเล่นจริง
ทดลองเล่นสล็อต pg
สล็อตออนไลน์ยุคใหม่กำลังยกระดับจากเกมหมุนวงล้อทั่วไปไปสู่ระบบออนไลน์ที่ใช้เทคโนโลยีขั้นสูง ซึ่งให้ความสำคัญกับการเชื่อมต่อ API โดยตรงร่วมกับระบบหลังบ้านที่ตอบสนองรวดเร็ว ผู้เล่นจำนวนมากเริ่มมองหาแพลตฟอร์มสล็อตเว็บตรง เพราะระบบทำงานลื่นกว่า และช่วยลดปัญหาความล่าช้า การค้างของเกม รวมถึงความล่าช้าในการอัปเดตยอดเงิน
ระบบสล็อตเว็บตรงจะรับส่งข้อมูลกับระบบของผู้พัฒนาเกมผ่านโหนด API ที่ไม่ผ่านตัวกลาง ทำให้ธุรกรรมของผู้เล่นถูกส่งแบบอัตโนมัติโดยไม่ต้องผ่านตัวกลางหลายชั้น ส่งผลให้เกมเปิดได้เร็วขึ้น ลดความผิดพลาดระหว่างการหมุน และช่วยให้ระบบแจ็คพอตทำงานได้ต่อเนื่องกว่าเดิม
อีกหนึ่งองค์ประกอบที่ทำให้ระบบนี้น่าสนใจคือระบบฝากถอนอัตโนมัติ ผู้เล่นสามารถเติมเครดิตและถอนเงินได้ตลอด24 ชั่วโมง โดยไม่จำเป็นต้องพึ่งพาระบบตรวจสอบแบบเก่าเหมือนเว็บที่ไม่มีระบบอัตโนมัติเต็มรูปแบบ ทำให้การควบคุมยอดเงินมีความรวดเร็วกว่าเดิม
สาเหตุที่สล็อตเว็บตรงได้รับความนิยมคือความโปร่งใสและความเสถียรในการเชื่อมต่อ เซิร์ฟเวอร์ที่ส่งข้อมูลไปยังผู้ให้บริการเกมโดยไม่ผ่านตัวกลางช่วยลดความไม่แน่นอนของระบบตัวกลาง ผู้เล่นจึงเข้าใจได้ว่าผลลัพธ์ของเกมมาจากกลไกสุ่มของค่ายเกม
นอกจากนี้ เว็บสมัยใหม่ยังมีการพัฒนาUX/UI สำหรับมือถือโดยเฉพาะ เช่น โหมดจอมือถือแนวตั้ง การเปิดหน้าเกมโดยไม่หน่วง และระบบกู้คืนสถานะเกมที่ช่วยคืนสถานะเกมเมื่อสัญญาณขาดช่วง
ผู้ให้บริการสล็อตสมัยใหม่เริ่มใช้AI วิเคราะห์ข้อมูล ร่วมกับระบบประมวลผลบนคลาวด์และAPI Syncเพื่อรองรับการเล่นต่อเนื่องของผู้เล่นหลายกลุ่ม บางระบบยังรองรับBlockchainเพื่อเพิ่มทางเลือกในการทำธุรกรรมและลดการพึ่งพาช่องทางการเงินแบบเก่า
ตลาดสล็อตออนไลน์จึงกำลังพัฒนาจากเว็บสล็อตทั่วไปไปสู่โครงสร้างเกมออนไลน์ที่เน้น API และเซิร์ฟเวอร์ โดยความเสถียรและประสบการณ์ผู้ใช้กลายเป็นปัจจัยสำคัญในการตัดสินใจใช้งานเว็บสล็อต
เมื่อการแข่งขันสูงขึ้นแพลตฟอร์มสล็อตจะยิ่งแข่งขันกันด้านประสิทธิภาพของระบบมากขึ้น ไม่ว่าจะเป็นการกู้คืนสถานะเมื่อระบบหลุด เครื่องมือวิเคราะห์ข้อมูลผู้ใช้งาน หรือการป้องกันข้อมูลส่วนตัว ผู้ให้บริการที่มีAPI เชื่อมต่อโดยตรงและเชื่อมต่อกับค่ายเกมโดยตรงจะแข่งขันได้แข็งแรงกว่าเว็บทั่วไปที่ยังใช้ระบบตัวกลางหลายชั้น
คนที่เลือกแพลตฟอร์มอย่างจริงจังจึงไม่ได้มองแค่ของแจกอีกต่อไป แต่เริ่มให้ความสำคัญกับความเสถียรของระบบ ความไวของการฝากถอน และความลื่นของเกมระหว่างใช้งาน
courtier immobilier Proprio Direct NDG
https://houseedge.us/games/slots/
https://winradar.us/casinos/
https://gorod-lugansk.ru/user/FrederickEbersba/
世界盃
2026 年世界盃 將由 48 個國家代表隊 角逐冠軍,整體賽程包含 12 個小組,每組 4 隊。小組前二名球隊 能夠進入 淘汰賽階段,展開 16 強至決賽的淘汰賽程。
這屆 FIFA 世界盃 會在 2026 年 6 月 正式開賽。首場比賽 預計由 墨西哥迎戰南非,於 6 月 12 日 在 Estadio Azteca 舉辦。同日後續賽程中,南韓將迎戰捷克。接下來一天,加拿大對波士尼亞,以及美國對巴拉圭等小組賽首輪賽事將登場。
分組名單顯示,A 組 由 墨西哥、南非、南韓與捷克;B 組 包含 加拿大、波士尼亞、卡達與瑞士;C 組 則是 巴西、摩洛哥、海地與蘇格蘭組成。像是 巴西、法國、阿根廷、西班牙、英格蘭與德國等傳統強隊 都已確定分組結果。
後續淘汰輪次 將於 7 月初 展開,16 強賽 預計從 7 月 4 日 登場,而冠軍戰預定於 7 月 19 日 上演,屆時將決定 2026 年 FIFA 世界盃冠軍。
歷史交手紀錄顯示,墨西哥過去曾與南非於 2010 年世界盃 交手,當時雙方以 1 比 1 握手言和,至今未分勝負。
另外,足球比賽規則如越位、黃牌、紅牌、VAR 與點球判罰,仍是球迷觀賽時的重要基礎知識,相關規則也持續受到關注。
FIFA世界杯
2026 世界盃 預計由 48 個國家代表隊 參賽,整體賽程包含 12 個小組,每組 4 隊。每組排名前兩位的隊伍 將晉級 淘汰賽階段,進行 後續淘汰賽與冠軍爭奪戰。
本屆世界盃 預計在 2026 年 6 月 正式開賽。開幕賽事 預計由 墨西哥對上南非,於 6 月 12 日 於阿茲特克球場開打。同一天稍後,南韓將迎戰捷克。接下來一天,加拿大將迎戰波士尼亞,而美國則對上巴拉圭。
小組賽方面,A 組 包含 墨西哥、南非、韓國及捷克;B 組 包含 加拿大、波士尼亞、卡達以及瑞士;C 組 包含 巴西、摩洛哥、海地及蘇格蘭構成。例如 巴西、法國、阿根廷、西班牙、英格蘭與德國等傳統強隊 已確認所屬小組。
後續淘汰輪次 預計於 7 月初 開始,16 強賽 大約在 7 月 4 日 開始,最終決賽將在 7 月 19 日 進行,並誕生 2026 世界盃冠軍隊伍。
從過往戰績來看,墨西哥和南非曾在 2010 年世界盃 對決,結果雙方踢成 1 比 1,雙方仍無勝場差距。
此外,足球比賽規則如越位、黃牌、紅牌、VAR 與點球判罰,也是觀眾理解比賽的重要基礎,相關規則也持續受到關注。